Structure, Size, and Reporting Lines
In this section, we report on department and unit work structures and size (i.e., positions created and eliminated), number of full-time positions budgeted for in cybersecurity and privacy departments and units, and whom respondents report to versus whom they believe they should report to.
Many work in a unit or department that includes cybersecurity. We asked respondents what type of department and/or unit they work in or lead (they could select all that apply):
- A unit dedicated to cybersecurity
- A unit dedicated to privacy
- A department that includes cybersecurity and other units (but not privacy)
- A department that includes privacy and other units (but not cybersecurity)
- A department that includes only cybersecurity and privacy
- A department that includes cybersecurity and privacy and other units
- Other
Overall, a large majority (86%) selected a single option, and most of these indicated that they work in a unit or department that includes cybersecurity. Breaking this down further, 41% work in or lead a unit or department that includes cybersecurity but not privacy, and 41% work in or lead a department that includes both cybersecurity and privacy. Few respondents (8%) were part of a unit or department that included privacy but not cybersecurity.
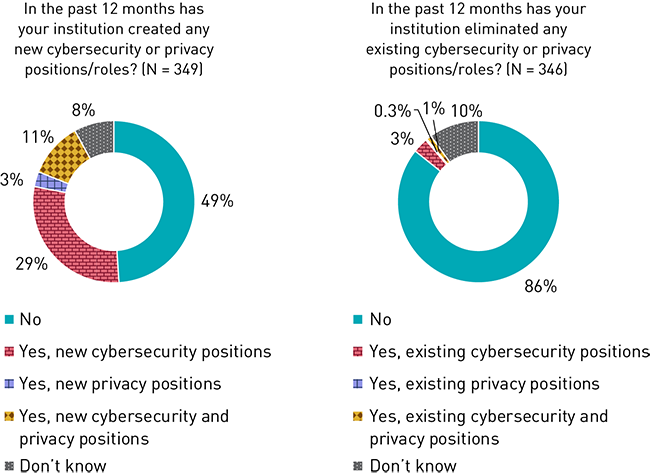
The cybersecurity workforce is more robust than the privacy workforce. We asked how many full-time equivalent (FTE) cybersecurity and privacy positions are budgeted for the current fiscal year. The average number for cybersecurity positions was five, compared to two for privacy. These numbers varied by institution size and type, especially for cybersecurity positions (i.e., doctoral institutions and institutions with larger enrollments had more positions budgeted). Further, fewer than half of respondents said that their institution has a role dedicated to privacy (40%). When asked about the creation and elimination of positions, 29% said that new cybersecurity positions were created in the past 12 months versus 3% who said new privacy positions were created (see figure 3). Overall, a majority (86%) of respondents said that no existing cybersecurity or privacy positions had been eliminated. Finally, in addition to more budget for and growth in cybersecurity positions than privacy positions, they also saw the most services outsourced: 36% of respondents said that their institution has outsourced cybersecurity services in the past 12 months, while only 6% said privacy services had been outsourced.
Most directly report to the CIO or CISO. Across all position levels, a majority (42%) of respondents said that they report directly to their CIO (see figure 4). Only a small percent of respondents (9%) said they report directly to the president, chancellor, or CEO, and most of these were C-level executives. A significant number of respondents said they reported to a person not listed in the survey response options (29%); these individuals indicated the person whom they directly report to, and a majority said they report to the CISO. Other respondents said they reported to technology leadership and management, compliance and governance leadership, and academic and departmental leadership.
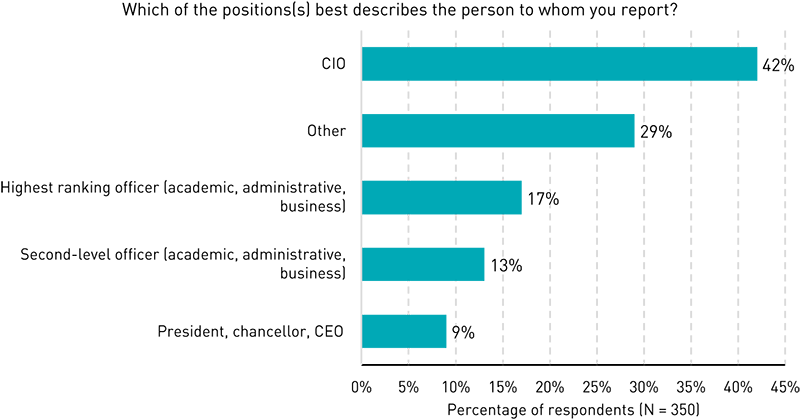
Some believe that they should be reporting to non-IT leadership. We asked respondents whom they think they should report to, and 27% identified someone other than whom they currently report to. Of these respondents, many (65%) indicated that they believe they should report to the president, chancellor, or CEO, and 23% said they should report to the highest-ranking administrative officer. A majority of those who thought they should have a different reporting line said that reporting to leadership outside IT would be appropriate due to a misalignment in goals and conflicts of interest between IT and cybersecurity or privacy. These respondents also noted that reporting to top-level (non-IT) leadership would be necessary to ensure that cybersecurity and privacy initiatives are aligned with high-level strategic priorities and goals and to ensure that cybersecurity and privacy are prioritized, given how crucial they are to institutional success.
CIOs and CISOs are at odds with each other with respect to mission. Since CISOs report to CIOs, there is a built-in conflict of interest with no conceivable solution.
Information security is not an IT problem, though it has a strong technology element. Coming from the private sector, I've seen countless InfoSec failures tied back to technology due to conflicting priorities for the CIO, and lack of direct tie-ins between security/compliance and business drivers.
Cybersecurity in our organization is multifaceted, involving compliance, IT, legal, and procurement. Reporting to the CIO boxes the team into a majority of IT duties and does not allow us to address other areas of impact.
If I were to report to the president, I would have access to information about the university's strategic priorities, and this would better enable me to focus my efforts to produce real value in the areas of greatest importance.
Cybersecurity is critical to the full functioning of the university. The president and provost need to equally understand any issues that arise and the impact on both the academic and operational parts of the university.
Privacy should have direct reporting to the highest or second highest level of accountability position within an organization in order to ensure privacy is paramount to the organization.