General Experience of IT on Campus
Overall Technology Experience
Faculty are, by and large, quite happy with the technology and support at their institution. In response to a question asking faculty to describe their overall technology experience at their institution,1 71% of respondents rated their experience as good or excellent and only 16% as fair or poor, as shown in figure 1.
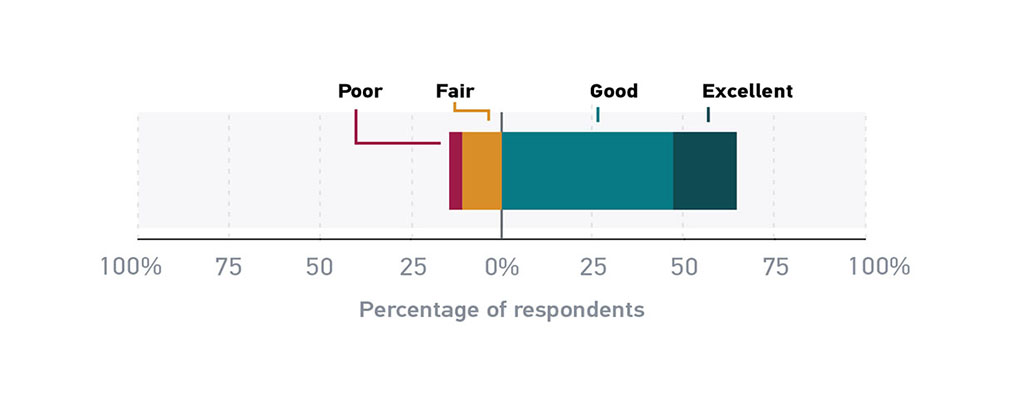
Respondents at associate’s and bachelor’s institutions are significantly more satisfied with the technology and support at their institution than respondents at master’s and doctoral institutions. The reason for this is not clear. As will be discussed below, no Carnegie class of institutions is more likely than any other to provide computing devices to their faculty, nor are faculty at any specific class of institution much more likely to use their institution’s IT help desk. Somewhat more surprisingly, there were no significant differences in the level of satisfaction between full- and part-time faculty or among different academic ranks.
Faculty members’ level of satisfaction with the technology experience at their institution does, however, vary by where they go for technology support. Faculty who seek technical support from the institution’s help desk are the most likely (76%) to rate their overall technology experience at their institution as good or excellent, while faculty who seek technical support from their friends or their students are the most likely (20%) to rate their overall technology experience at their institution as fair or poor. Note that in the “Technical Support” section, below, it is reported that the help desk topped the list for where faculty seek technical support; “Ask friends” was near the bottom. “Ask teaching or research assistants” was at the very bottom of the list, though most faculty who seek technical support from those individuals rate their overall technology experience at their institution as good or excellent (71%). This last finding may indicate a partly hidden function of teaching and research assistants as more or less informal providers of tech support to faculty. It might benefit institutional IT departments to reach out to and provide technology training to teaching and research assistants in an effort to “train the trainers.” Any such training that teaching and research assistants receive is likely to benefit faculty later.
Technical Support
Respondents were asked: “When you need technology support or assistance for work-related activities, what do you typically do?” A list of nine items was provided, and respondents could select up to three. The first thing to notice about figure 2 is the two very clear groups of responses: Nearly half to three-quarters of respondents selected the items in the first group, while fewer than 10% of respondents selected the items in the second group. These two groups are clearly distinguished by their relative levels of perceived expertise. It is not clear in what order faculty seek information from these sources, what sources they consult first, second, third, etc. Nevertheless, most faculty seek information from sources that they perceive as having expertise, such as their institution’s IT help desk, their colleagues, or themselves. All other information sources come in a distant second.2
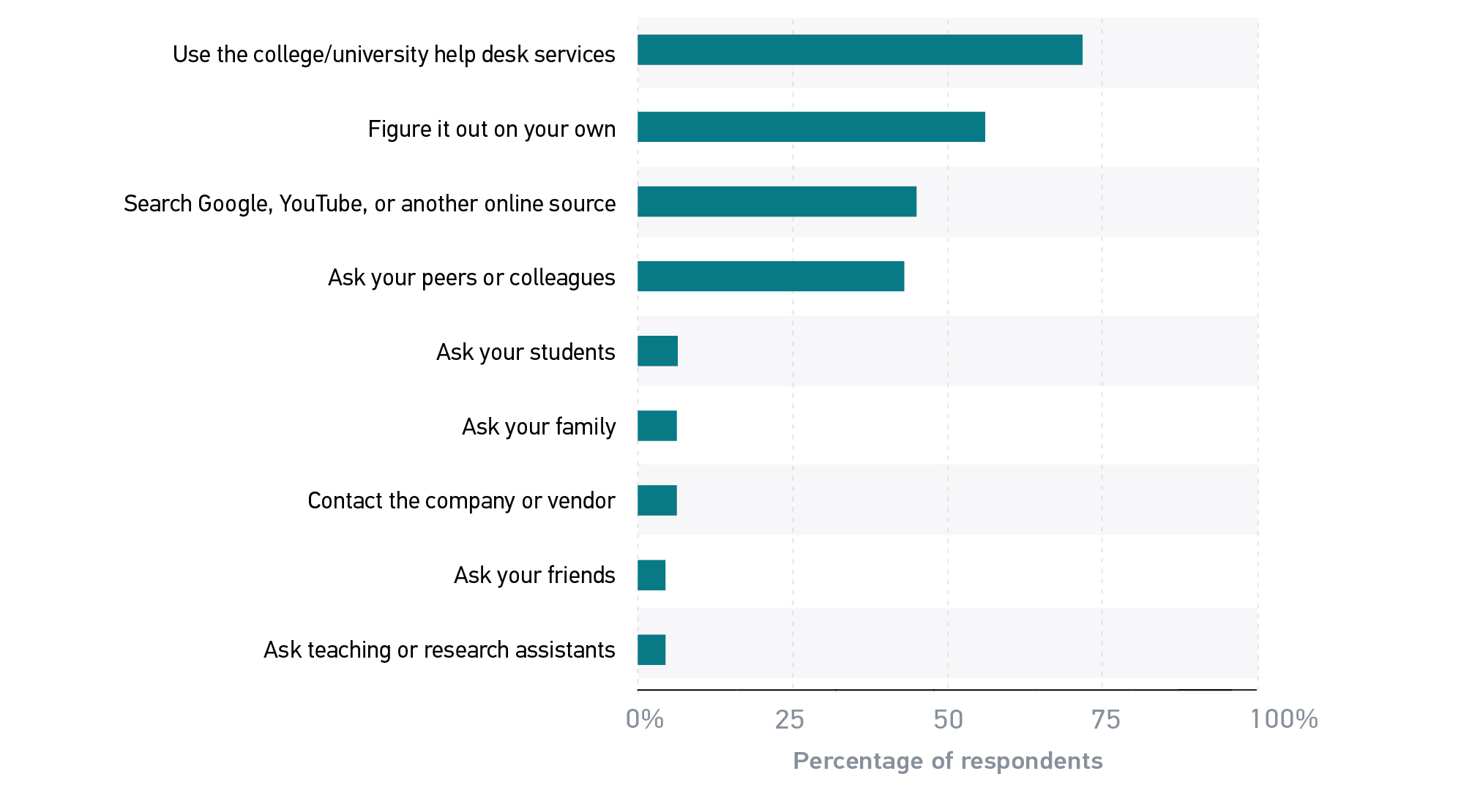
Faculty, of course, operate in a reputation economy in which reputation is largely based on expertise. So it is no surprise that faculty prioritize information sources that they perceive as signifying expertise and deprioritize other sources.3 A faculty member’s perception of expertise may be incorrect: Students or research assistants, for example, may in fact have quite a bit of knowledge about certain IT issues, and a company may be the best source of information about its product; but that is not the point. While an information seeker may fail to appreciate the existence of an information source, perception is reality here: Faculty prioritize sources of perceived expertise, particularly when that source of expertise is themselves or their colleagues. Decades of research exists on information-seeking behavior and the information search process,4 much of which shows that the principle of least effort applies to information seeking,5 as it does in so many other arenas. It is possible to move beyond simple satisficing in information seeking, but this requires experience.6 Faculty, of course, gained that experience thanks in part to years of training in graduate school, and thus it has become second nature for faculty to rely on and trust expertise.
These findings have clear implications for institutions’ IT help desks. Many help desks are in libraries or other locations that are intended to be convenient for students. However, a far greater percentage of faculty than students use their institution’s help desk.7 It is not clear from this survey how faculty are making use of the help desk, but it seems likely that more faculty members’ use is mediated (phone, e-mail, etc.) than in person (at the desk). Therefore, campus IT units need not necessarily gear their help desk service toward faculty but should at least provide significant support to faculty for the types of issues that they are likely to encounter (e.g., assistance with LMS functionality, connecting to institution-provided services while traveling). At many institutions, IT support is distributed across academic units—a hybrid of centralized and decentralized;8 these local help desks are in a good position to develop customized support services.
These findings also have clear implications for faculty themselves. Any help that a faculty member receives from the help desk, or training from any source, not only helps that faculty member individually but also potentially helps that faculty member’s colleagues later. The IT units in institutions of higher education would therefore do well to provide and promote training to faculty. Such training or workshops will not only directly benefit the recipients but are also an opportunity to “train the trainers,” as faculty are likely to pass their knowledge along to their colleagues.9
Information Security at the Institution
One type of training that IT units provide to everyone at the institution is on information security. Respondents were asked a series of questions about this type of training. The first of these questions was whether the institution provides information security training, either mandatory or optional. The findings from this question were perhaps the most staggering of this entire series: As shown in figure 3, fully 48% of faculty do not know if their institution provides information security training.
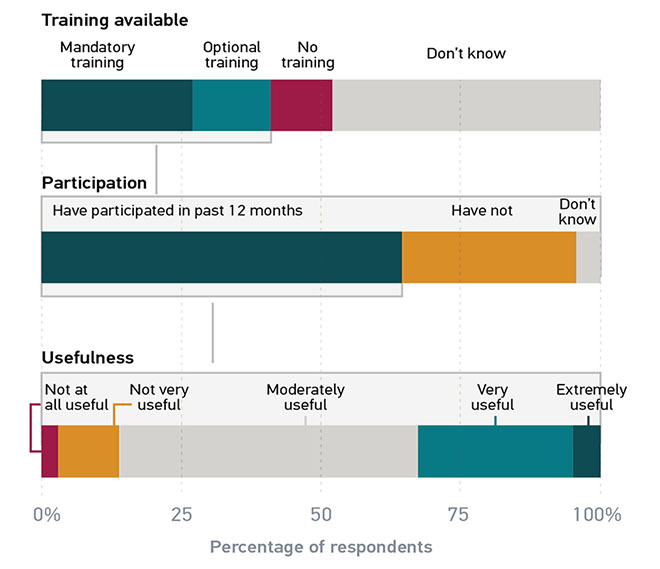
Respondents who answered in the affirmative, for either mandatory or optional training, were then asked whether they had participated in this training in the past 12 months. Approximately a third of respondents whose institution offers information security training have not participated in it in the past 12 months, while two-thirds have. This breaks down further: 81% of respondents whose institution’s information security training is mandatory have participated in this training in the past 12 months, but only 30% of those whose institution only offers optional information security training have. Unsurprisingly, if information security training is optional, then most faculty members will not participate. It is also possible, of course, that some institutions do not require information security training for faculty every year, so even if it is mandatory, some respondents may not have participated in the past 12 months. Yet a third possibility is that faculty simply may not feel that they need information security training.
Respondents were asked a small set of questions about their level of confidence in their institution’s information security practices and its ability to safeguard a variety of types of information.10 By and large, faculty have a great deal of trust in their institution’s information security practices: Between two-thirds and three-quarters of respondents agreed or strongly agreed that they have confidence in their institution’s ability to safeguard information. This is consistent with the results of the 2015 faculty survey,11 with one notable exception: A far greater percentage of respondents (an increase of nearly 30 percentage points) agreed or strongly agreed that they “understand relevant university policies” about data storage in 2017 than did so in 2015. This speaks well of efforts by campus IT units to communicate policies over the past two years.
Perhaps the most important finding from this set of questions, however, is that 63% of faculty disagreed or strongly disagreed that their institution’s security policies impede their productivity. In other words, institutional security policies are more or less invisible to most of our respondents. This finding could be read as indicating that faculty have confidence in their institution’s information security practices as long as the policies that enable them are more or less invisible. Furthermore, as long as their institution’s security policies are invisible, faculty do not believe that they need training in these policies.
Returning now to the questions about information security training, respondents who answered that they had participated in their institution’s information security training in the past 12 months were asked a third question: How useful was this training?12 Perhaps unsurprisingly, the most common response to this question (54%) was the midpoint of the scale, “Moderately useful.” However, approximately a third of respondents found this training very or extremely useful.
Finally, respondents who answered that their institution’s information security training was not very useful or not at all useful were asked a final, open-ended question: How can your institution make information security training more useful? As might be expected, since only those who responded to the previous question negatively were asked, the responses to this question were quite negative. Nevertheless, these responses yielded some useful and actionable advice. One prevalent theme in these responses was a sometimes quite intense dislike of third-party training videos. In some cases, respondents indicated that these videos were outdated, which significantly blunted the impact of their message. Some respondents indicated that the information in these videos was common sense (such as how to create secure passwords13) and thus came across as condescending. Several respondents suggested that written documents could convey the same information in less time and less irritatingly. Many more suggested that live training sessions, offered in person and in a classroom, would be far better received.
An equally important theme in these responses was customizing the training for the institution, for the discipline, and for the types of data collected by and activities being performed by the faculty member.14 Many respondents suggested that the training was too general to be useful and that they would appreciate specific recommendations for tools they can use, beyond simply installing the institution’s enterprise-scale security software suite. They wanted specific policies that they can follow in specific contexts, and information on how to identify security concerns such as fraudulent e-mail and security breaches. A few respondents found the training too technical, though a far greater number wrote that, as experienced technology users, they found it too simple. Many of these respondents suggested that there should be more advanced levels of training and that one should be able to opt out of more basic levels. Several respondents were clearly faculty in humanities disciplines because a small but important theme that emerged was that much of this training is oriented toward securing research data and has little to say about the more creative work that might be produced by faculty in, for example, a creative writing or graphic arts department. These examples emphasize the need for institutions (or for organizations from which institutions license or purchase such training) to customize information security training, not merely to keep the content relevant and up to date but to ensure that the message of the training is heard at all.
Device Ownership
IT is integrated into nearly every aspect of higher education, so it is critical for faculty to have access to devices for their personal and professional use. Respondents were asked if they personally own, or if their institution provides them with, any of a small set of common types of devices.15 Figure 4 shows a finding similar to what ECAR found in 2015, that laptops continue to be the workhorse for faculty, with fully 97% of faculty having one (combining both those provided by the institution and those personally owned).16 Desktops aren’t far behind, with 85% of faculty having one (again, combining institutional and personal ownership). Those laptops and desktops are provided by the institution to more than half of our respondents, with desktops having the edge over laptops (61% to 51%). The percentage of respondents’ institutions that provide laptops is up slightly from the 2015 faculty study.17
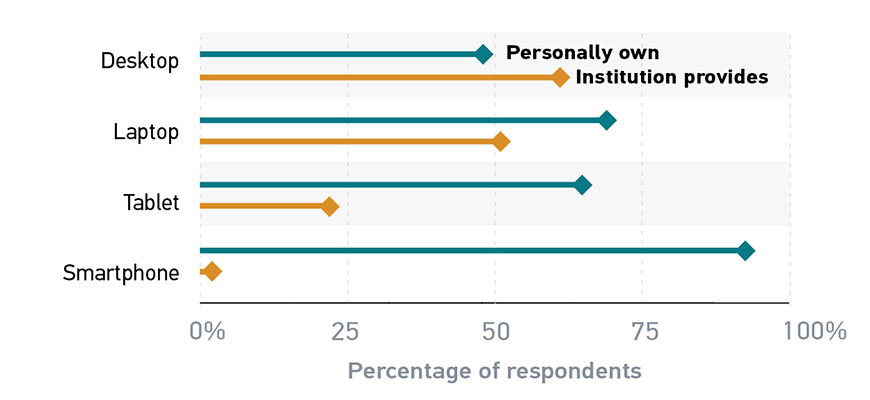
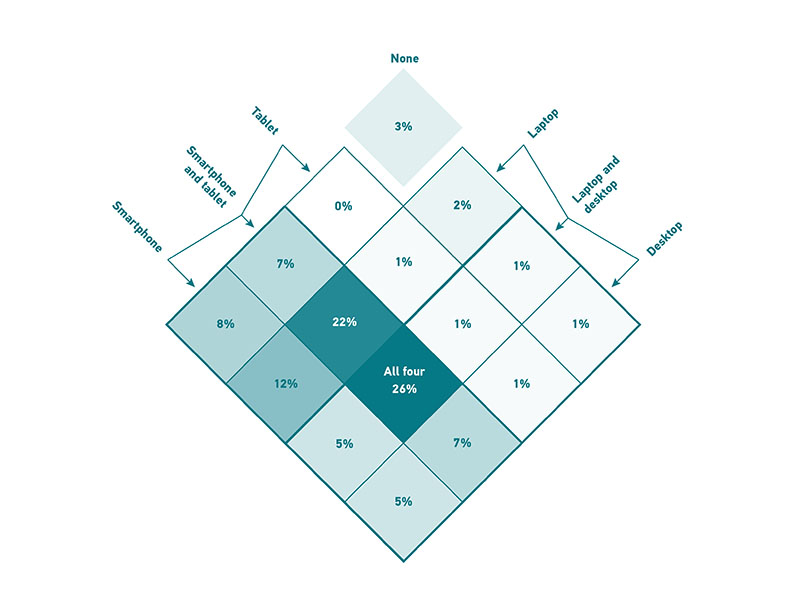
Figure 5 shows data on which of these same devices faculty personally own. To read this figure, follow the arrows from the devices diagonally across and down. Most cells in this grid are an intersection: 5% of faculty personally own both a desktop and a smartphone, 12% of faculty own both a laptop and a smartphone. Fully 26% of faculty own all four devices, and 22% own a laptop, a smartphone, and a tablet. Fewer than 1% of faculty own only a tablet, and, somewhat surprisingly, 3% of faculty own no devices at all.
While no Carnegie class of institutions is more likely than another to provide devices to their faculty, there was some variation across disciplines. Faculty in disciplines that are traditionally vocational but with the advent of data science are becoming increasingly computerized (e.g., agriculture and natural resources; and manufacturing, construction, repair, and transportation) are the most likely to have desktops and laptops provided by their institution, while faculty in the humanities (e.g., liberal arts, fine and performing arts) are the least likely. Somewhat surprisingly, disciplines generally thought of as requiring high-performance computing (e.g., computer science and engineering) were solidly in the middle of this list. This latter finding may reflect the fact that these disciplines do require high-performance computing and therefore some faculty in those disciplines may provision their own hardware through grant funding rather than work with an institutional standard device inadequate to their computing needs.
The predominant operating system on devices owned by faculty is Windows (75% of desktops, 63% of laptops), though there is a solid contingent of Mac users (21% of desktops, 33% of laptops). Linux and Chrome OS have small but presumably very loyal user bases: Linux accounts for 2% of desktops and 1% of laptops, while Chrome OS accounts for 2% of both.
Many faculty buy their own personal laptops despite being provided with hardware by their institution. Of faculty who were provided with a desktop by the institution, about 73% also own a personal laptop. Of faculty who were provided with a laptop by the institution, about 45% own another personal laptop. Depending on where the faculty member uses this personal laptop, and for what purposes, this raises the potential for security risks to the institution’s network, as the personal laptop may not have installed whatever suite of security tools the institution provides.
The finding that more faculty personally own laptops than desktops is consistent with device ownership trends found in different contexts. The Pew Research Center found that in the United States at large, laptop ownership surpassed desktop ownership in 2011.18 That laptops are increasingly the preferred “heavy” device for personal ownership perhaps reflects the increasingly mobile nature of computing generally. This is borne out by the slight increase since the 2015 faculty survey in the percentage of faculty owning “light” devices such as tablets and smartphones. Smartphones in particular are becoming ubiquitous, with 93% of faculty personally owning one. Despite this, however, 22% of respondents say they are provided a tablet by their institution, while only 2% are provided a smartphone.
As discussed above, most institutions of higher education provide a laptop or a desktop to faculty. This makes sense, given that these devices remain more able than tablets and smartphones to support certain categories of complex applications, such as statistical analysis software; they also tend to be easier to use for production work, such as writing and grading papers. Given that the job of faculty involves a great deal of both writing and grading, institutional support for these “heavy” devices continues to make sense. But here there is an interesting crossover with the findings from the 2017 student study: Fully 83% of students used a smartphone for course-related activities for one or more of their courses, and 25% used a smartphone for all of their courses; two-thirds of students consider it very or extremely important to be able to use a smartphone for course activities. Given that students are so extensively using handheld devices for course activities, it may be worthwhile for institutions of higher education to consider providing (or sharing the cost of) such devices to faculty, so as to better enable faculty to support students on the platforms and in the environments where they are.
Notes
-
Responses to these questions were on a 5-point Likert-type scale, ranging from “poor” to “excellent.”
↩︎ -
Responses to this survey question do not sum to 100%, as respondents could select up to three items.
↩︎ -
This behavior is consistent with “cognitive miser theory,” according to which, in order to reduce the cognitive load of day-to-day decision making, individuals take mental shortcuts. Relying on sources of perceived expertise is one such shortcut that faculty would be likely to make. See Susan T. Fiske and Shelley E. Taylor, Social Cognition (2nd ed.) (New York: McGraw-Hill, 1991).
↩︎ -
T. D. Wilson, “On User Studies and Information Needs,” Journal of Documentation 37, no. 1 (1981): 3–15; C. Kuhlthau, Seeking Meaning: A Process Approach to Library and Information Services (London: Libraries Unlimited, 2004).
↩︎ -
K. E. Fisher, S. Erdelez, and L. McKechnie, eds., Theories of Information Behavior (Medford, N.J.: Information Today, Inc., 2005).
↩︎ -
Claire Warwick, Jon Rimmer, Ann Blandford, Jeremy Gow, and George Buchanan, “Cognitive Economy and Satisficing in Information Seeking: A Longitudinal Study of Undergraduate Information Behavior,” Journal of the American Society for Information Science and Technology 60, no. 12 (December 2009): 2402–2415; Chandra Prabha, Lynn Silipigni Connaway, Lawrence Olszewski, and Lillie R. Jenkins, “What Is Enough? Satisficing Information Needs,” Journal of Documentation 63, no. 1 (2007): 74–89.
↩︎ -
D. Christopher Brooks and Jeffrey Pomerantz, ECAR Study of Undergraduate Students and Information Technology, 2017, research report (Louisville, CO: ECAR, October 2017).
↩︎ -
Karen A. Wetzel and Jeffrey Pomerantz, Organizational Models for IT Service Delivery and the Evolving IT Organization, research report (Louisville, CO: ECAR, August 2016).
↩︎ -
The institution at which one of our external reviewers for this report series works implemented a creative and effective “train the trainers” program. During the institution’s recent migration from one LMS platform to another, the IT unit designated a faculty member in each academic unit as the first line of support and provided extra training and—importantly—stipends for these faculty. These faculty members invited their colleagues to join them in a classroom prior to the start of the semester and helped everyone set up their courses for the first time in the new LMS platform.
↩︎ -
Responses to this question were on a 5-point Likert-type scale, ranging from “strongly disagree” to “strongly agree.”
↩︎ -
D. Christopher Brooks, with a foreword by John O’Brien, ECAR Study of Faculty and Information Technology, 2015, research report (Louisville, CO: ECAR, October 2015).
↩︎ -
Responses to this question were on a 5-point Likert-type scale, ranging from “not at all useful” to “extremely useful.”
↩︎ -
Even what passes for “common sense” in creating secure passwords is actually poor information security practice. Robert McMillan, “The Man Who Wrote Those Password Rules Has a New Tip: N3v$r M1^d!,” Wall Street Journal, August 7, 2017; Nick Statt, “Best Practices for Passwords Updated after Original Author Regrets His Advice,” The Verge, August 7, 2017.
↩︎ -
Rachael Gabriel, “The Case for Differentiated Professional Support: Toward a Phase Theory of Professional Development,” Journal of Curriculum and Instruction 4, no. 1 (2010).
↩︎ -
Responses to this survey question do not sum to 100%, as respondents were asked to select all that apply.
↩︎ -
D. Christopher Brooks, with a foreword by John O’Brien, ECAR Study of Faculty and Information Technology, 2015, research report (Louisville, CO: ECAR, October 2015).
↩︎ -
In the 2015 faculty study, 48% of respondents’ institutions provided laptops.
↩︎ -
Since 2011, the Pew Research Center and the U.S. Census have both combined laptop and desktop ownership into a single category of device ownership. See Mobile Fact Sheet from the Pew Research Center.
↩︎