The Gathering Cloud: Is This the End of the Middle?
The Gathering Cloud: Is This the End of the Middle?
"… it is clear that technology allows institutions to blur, if not erase, institutional boundaries once clear and distinct."
—Steven Crow, former president, Higher Learning Commission of the North Central Association of Colleges and Schools
H. G. Wells described human history as a race between education and catastrophe. If this is so, higher education has played a major role in safeguarding the world. In the West, educators often trace their professional origins to Plato’s academy, where skeptics reasoned and reflected on goodness and knowledge. Platonic education was personal, eschewing even the written word. Socrates described writing as an “invention [that] will produce forgetfulness in the souls of those who have learned it.”1 In early modern Europe, itinerant educators traveled to students who pooled resources to pay for their tuition.2
The 11th and 12th centuries represent a turning point in the history of higher education, with the founding of the College de Sorbonne, Oxford University, the University of Salamanca, the University of Bologna, and the University of Modena and Reggio Emilia. Universities in the West assumed the physical form that we recognize today and operated under papal or royal charters. The Western form of universities and colleges is resilient. Many institutions have served their societies through natural disasters, times of war, revolution, economic turmoil, and political upheaval. In many cases, our oldest universities have persisted longer than the nation states, forms of government, and royal houses that chartered them. They have grown in number, size, and influence, bearing witness to Wells’s lament.3
Fiat Lux
Ten threads have influenced the makeup of Western higher education’s tapestry in this millennium.
1. The academy is an artisan community. The Western university and college is a clear outgrowth of medieval monastic and guild life. Like guilds and monasteries, the modern academy consists of communities that “comprise the enduring interpersonal relations that form around shared practices.”4 Brown and Duguid argue that successful academic communities are inhabited by people who share common tasks, obligations, and goals.5 As with medieval guilds, modern professors enculturate their students to the language, syntax, methods, and resources of an academic discipline as well as connect students with other scholars in the community. Students (apprentices), like their medieval guild counterparts, look to older students (journeymen) for instruction, to peers for edification and affirmation of practice, and to professors (masters) for endorsement and acceptance. The craft origins of higher education are evident in our cottage-industry modes of research and instructional production. To a very great extent, research funding flows to individual researchers from sponsors outside the academy’s walls, and the key decisions about the scope, methods, time frames, and goals of research are set and enforced by individual investigators. In instruction, academic courses are typically crafted by individual instructors and are rarely shared among other academics who share similar—or even identical—responsibilities.
2. Academic practice is organized around scarcity. The modern Western university and college evolved to a great extent from the libraries and scriptoria of the 6th century, which served to select, collect, copy, preserve, and protect the textual record of European life. The crafts of writing and illuminating manuscripts and written materials themselves were rare, and early academic institutions were designed to protect and preserve scarce people and objects and to mediate access to scarce resources. Early institutions operated more as knowledge and learning filters than as pumps. Books were chained and locked away in towers. Higher education’s emphasis today on openness reflects both the growing abundance of knowledge and knowledge work and a relatively recent understanding that widespread education is an engine of progress and human development.
3. The academy is a place. Since the 12th century, higher education has been a place. Students “go to college.” Scarcity drove the early need for space and early colleges and universities were built as a means of attracting scarce people of intellect to one another and to the scarce raw materials of scholarship (books, laboratories, surgical theaters). These were not humble beginnings. In keeping with their papal or royal charters, early universities were often beautiful places. The medieval idea of the university as a majestic and cloistered place designed to foster fellowship, collegiality, reflection, and independence is deep seated. It is reinforced in literary and film treatments of higher education and has influenced generations of architects and campus planners. Even campuses in virtual worlds such as Second Life and elsewhere draw inspiration from the medieval idea of a city of intellect featuring sacred gardens and other spaces to be secured by walls, gates, and towers. Medieval universities—and many modern ones—were designed to be places apart from the rude and cacophonous rabble, places of quiet and beauty, ripe for reflection, discussion, inquiry, and discovery.
4. Academic governance has devolved. Before colleges and universities were chartered by civil or ecclesiastical powers, students pooled their financial resources to bring learned men to their cities and towns. By the 11th century, place-based institutions largely displaced these practices. The power and influence of the student guild declined. Over time, authority over many universities passed to local authorities, and ultimately universities became self-governing corporations. A unique aspect of university self-governance is the division of responsibilities among administrators for the material sustenance of the institution and among the academics for the intellectual welfare of the academy and its citizens. Student opinion continues to play a role in college and university decision making, but not to the extent found before the construction of the great universities.
5. Academic activities are bundled. Colleges and universities approach learning holistically. We speak of academic programs and of courses of instruction. We distinguish an educational experience from a training experience. Institutions strive not only to impart knowledge but to prepare enlightened citizens, engage members of their communities in the “life of the mind,” and enhance “every individual’s particular gifts, and voice, and promise.”6 Thomas Jefferson argued that “light and liberty go together.”7 Colleges and universities issue credentials designed to signal others about one’s standing as an educated apprentice, journeyman, or master in a domain of knowledge and practice. The holistic approach to education is a practical one. Modern academies seek wherever possible to leverage their faculty, libraries, and other resources. Bundling academic offerings into programs and courses of instruction enables (and masks) a complex system of cross subsidies that make it possible for institutions to provide for study in those disciplines that may be impractical or out of favor. This insulates colleges and universities to an extent from pressures to be fashionable. From a narrower consumer perspective, bundling allows these institutions to offer—or even require students to take—instruction they have available ratherthan instruction that students (or employers) may want.
6. The academic mission has three parts. From their inception, universities and colleges have mixed three missions. Instruction, research, and service have always been intertwined. Early academies featured surgical theaters, translation centers, clinics, and astronomical observatories. These institutions not only served the community of scholars but were important in spreading knowledge, in food production, in nautical exploration, in diplomacy, and in military applications such as ballistics. Research and service to society and to the institution’s political patrons have always been intertwined. Most academics believe that the elements that comprise higher education’s mission mutually reinforce each other.8
7. The academy has become more accessible. Ideas about enlightenment and citizenship fueled significant growth in colleges and universities in the 18th century, and access widened even more in the 19th century as the commercial application of scientific discoveries further enhanced the standing of higher education. Thomas Jefferson reflected that an aristocracy of virtue and talent would be essential to the functioning of a well ordered republic.9 In the United States, secondary school enrollments rose from 297,894 to 824,447 between 1890 and 1906 as a reflection of the rise in education’s perceived value.10 This expansion was echoed in higher education as U.S. postsecondary enrollments rose from 200,000 at the turn of the 20th century to more than 18 million today.11 As the wealth of nations and citizen prosperity have become closely associated with higher levels of educational attainment, many nations have opened higher education’s gates wider. Women, long denied access, now outnumber men in higher education throughout much of the developed world, and institutions such as the Open University and the University of Phoenix enroll more than 100,000 students, spanning multiple state and national jurisdictions. Colleges and universities no longer serve only elite populations and increasingly serve students of all ages and backgrounds.
8. Openness pervades academic inquiry. The history of Western higher education is a history of increasingly open inquiry. Early universities regulated as well as preserved knowledge. As colleges and universities won self-governance, academic freedom and openness have become values that are shared widely among members of the academy. Open inquiry is at the heart of scientific method, which makes sense of the world by making observations, forming and testing possible explanations of those observations, and repeating experiments over and over again. The process of structured scientific inquiry depends on an open and increasingly public iteration between observations and interpretations. Patterns of observations are socialized by the academic community and can thus suggest possible general principles that in turn are used to generate predictions about future observations. Openness is central to others’ ability to reproduce experimental results, and reproducibility is central to scientific research. To a great extent, academic scholarship is less about finding “truth” than it is a process of continual and open inquiry informed by curiosity, and skepticism.
9. The academy’s range is growing geographically. Colleges and universities have extended their geographic presence, influence, and footprint. By 2007, nearly 600,000 non-U.S. students enrolled in U.S. colleges and universities.12 U.S., British, and Australian universities have opened significant academic operations in the Middle East, India, Singapore, and elsewhere. A decade ago, Australia made exporting Australian higher education to international students a cornerstone of its education and trade policy. The importance of higher education has become widely understood throughout the world.13 The emergence of robust networks, collaborative tools, and rich digital stores of scholarly materials is making it possible to extend higher education to more and more people. As Thomas Friedman put it, “We are now in the process of connecting all the knowledge pools in the world together ... anyone with smarts, access to Google, and a cheap wireless laptop can join the innovation fray.”14
10. Scientific research is a catalyst of accelerating change. While the academy’s instructional mission is discharged today in ways that can be traced to medieval monastic or guild traditions, the organization and conduct of research—particularly scientific research—can be barely recognized from that of 100 years ago. Teams of researchers that extend across domains of expertise and national borders organize experiments using instruments of unimaginable size, power, and expense. The time scale from problem conception to experimentation to commercialization has collapsed. New fields of inquiry are born regularly, often requiring the emergence of new methods, a new language of description, and new conventions. Research output is breathtaking. In 2003 and 2004 there were more than 7,500 scientific journals, and the number of articles appearing in the top 16 of those journals alone in 2002 and 2003 was 6,911.15 Table 1 summarizes some of the key trends that can be traced in the history of Western higher education.
| Table 1. Key Trends in the History of Western Higher Education | |
| FROM | TO |
| Teaching is a small-scale craft and learning is personalized. | Instruction is a scalable craft and can be standardized, personalized, or self-guided. |
| The governing power of colleges and universities is derived from church or state. | Colleges and universities are largely self-governing. |
| The academy is isolated from society. | The academy is enmeshed in communities served. |
| College or university education is accessible to an elite student body. | College or university education is accessible to all capable. |
| The college and university service base is local. | The college or university service base can be local, regional, national, or global. |
| The college or university is a place. | The college or university is situated in a place and virtually enhanced. |
| Scholars and academic resources are scarce and inaccessible. | Scholars and academic resources are plentiful and easily accessible. |
| Colleges and universities are purveyors and collectors of knowledge. | Colleges and universities are creators of knowledge. |
| Colleges and universities are local. | Colleges and universities are increasingly global. |
The Gathering Cloud
While it took 1,000 years to raise the tower of higher education, it has taken only 60 years to launch the digital computing and communications revolution. And while the history of computing and communications is faster moving and more boisterous than the history of higher education, it is less subtle and therefore easier to tell. At the most fundamental level, the story of information and communication technology is that of a quest to put thinking and communicating power everywhere and in everything and to connect it all. This is being accomplished by making computers faster, cheaper, better, more reliable, smaller, and more personal; by making communication ubiquitous and fast; and by making connections persistent.
The fuller story is a rich tale of five eras of innovation, economics dominated by Moore’s law, and exponential improvements in performance.
Mainframe Computing
The mainframe era was launched in the 1940s with the appearance of computing behemoths named Mark I, ENIAC, EDVAC, and Manchester’s Baby. They were developed and housed in major research universities such as MIT, Harvard, the University of Pennsylvania, and the University of Manchester. These machines were enormous, cumbersome, and specialized. They were used chiefly for computationally intensive military applications such as ballistics.
The replacement of vacuum tubes with transistors in 1947 and the introduction of semiconductors in 1958 enabled cost-effective miniaturization, the proliferation of devices, and decreases in cost. Third-generation programming languages such as C, Basic, FORTRAN, ALGOL, and COBOL made it possible for computers to support an increasingly wide range of scientific and accounting functions. Large-scale computing is inherently expensive and complex and tends toward centralized management. Large computers, computer clusters, and associated storage devices require power, space, cooling, scientific and technical expertise, and physical security. Computation of this kind was expensive and therefore tightly controlled. And, of course, the mainframe—and later the minicomputer—was an island. While multiple monitors were multiplexed to mainframe computers in the 1950s, allowing more than one user to make use of a mainframe, this practice did not become commonplace until time sharing was successfully commercialized at Dartmouth in 1964.
Personal Computing
While the economics of semiconductors made it possible to develop relatively inexpensive minicomputers such as Digital Equipment Corporation’s PDP-8 (1965), the development of the home computer by Apple in 1977 and the personal computer by IBM in 1981 ushered in a new age of computing. These developments led Time Magazine to name the computer as its “Man of the Year” in December 1982.
The shift from large-scale to personal computing was revolutionary. In this era, Microsoft acquired QDOS and emerged as the dominant supplier of operating systems for computers of this kind. Within a year, the text and keyboard command-driven MS-DOS operating system were under pressure from graphical user interfaces (GUI) such as those demonstrated on the Apple Lisa. In 1983, Apple released the Macintosh along with the Orwellian Super Bowl television commercial suggesting the coming of a new age in computing. By late 1983, Microsoft announced Windows, an operating system that featured GUI and a multitasking environment for the IBM PC.
In higher education, the PC and its evolving operating system liberated computing from the data processing department in an unplanned fashion. Decentralized grant funding, in particular, resulted in a proliferation of personal computers throughout research universities and an associated proliferation of software applications, support organizations, and so forth. This unplanned technology archipelago gave rise to persistent IT governance challenges, inefficiencies, and risks. Notwithstanding these challenges, the personal computer put incredible capabilities into many people’s hands. Computers became the defining medium of work. And while early PCs were slow and cumbersome to use, they quickly became faster, easier to use, and more standardized and enjoyed the emergence of an extraordinary proliferation of software programs—many directed at improving professional productivity. IT research firm Gartner, Inc., predicts that there will be 2 billion computers in use worldwide by the year 2014—remarkable growth in less than 35 years.16
PCs in this era, like mainframes, were stand-alone devices, and early personal computing suffered from local suboptimization from the institutional perspective. Enterprise computing consisted of the financial system, the student system, and the payroll/personnel system. Research computing and most office work took place outside the gaze and purview of the campus IT organization.
Physical Connectivity
By 1969, host computers at UCLA, UC Santa Barbara, Stanford Research Institute, and the University of Utah were connected by a network developed by the Department of Defense (DOD). Over the next 15 years, ongoing innovations such as the development of Ethernet, Transmission Control Protocol (TCP), packet switching, and others resulted in the remarkable proliferation of networks and interconnection of computers and other devices. By 1971, 23 host computers were connected by networks, and by 1973, University College London became the first international host to be connected to the DOD’s ARPAnet. By 1984, the increasing adoption of Internet Protocol (IP) and other innovations fueled the accelerating growth of the network. The number of network host computers broke 1,000 that year. With the evolution of the domain name system, e-mail, file transfer protocol, newsgroups, and other enabling communication innovations, the computer became a communication device. In 1986, the 56Kbs NSFnet succeeded the ARPAnet, fueling greater demand for computer connections and paving the way for the growth of supercomputer centers at Cornell, Pittsburgh, Princeton, San Diego, and Urbana-Champaign. By 1987, the NSFnet was commercialized and more than 10,000 host devices were connected. By 1989, more than 100,000 host devices were connected to the NSFnet. Networks in Canada, Denmark, France, Iceland, Norway, and Sweden were connected to the U.S. network. By 1990, more than 1 million hosts were connected to the network. The invention of the World Wide Web meant that digital resources of many kinds could now be linked and displayed in common and easy-to-use ways that were also graphically rich. This invention fueled a rush to post and link an unprecedented volume of information online that shows no signs of abating. Search engines emerged in 1995 to help make it possible for people to gain unprecedented access to a wide variety of information resources by using language that was natural to them. The computer was now a communication device and the Internet and web, a mass medium.
Logical Connectivity
The extraordinary proliferation of computers in the 50 years between their invention and the middle of the 1990s, and the emergence of a global data communication network linking hundreds of thousands of users, created the possibility of doing things “anytime and anywhere.” In the United States, the NASDAQ stock exchange began trading over the Internet, lending legitimacy to business conducted over the network. By 1997, new standards (802.11) for connecting devices and networks wirelessly were approved and deployed over dedicated portions of the U.S. spectrum. At the same time, second-generation mobile telephone systems began to appear using TMDA and CMDA protocols. SMS messaging also emerged during this period. The message was clear—connectivity to networks was spreading like wildfire, and connectivity no longer depended on physically linking devices through wires or cables. These and subsequent innovations worked hand in hand with ongoing efforts to make intelligent devices smaller and faster, resulting in an explosion of intelligent and connected devices that were designed to travel with their owners. Computers no longer filled entire rooms; they fit inside pockets.
The connectivity associated with networks and the mobility associated with modern computing and storage devices have made “being digital” irresistible, and telephony, television, film, music, and video have raced to become part of an interconnected digital landscape that could only be characterized as a lifestyle. By 2000, wireless devices were in widespread use in Fortune 500 companies, and by this writing there are 220,000 wireless hot spots in the United States alone.17 The rapid deployment of new Wi-Fi standards and the global adoption of third-generation standards for cellular communications herald an age when it will be possible to remain persistently and logically connected to the Internet anywhere in the world.
Embedded Connectivity
As video, voice, and text have become increasingly digital, the focus of attention is on ubiquitous access and persistent connection. In such an environment, everyone may be connected all the time to a network that is linked essentially to everything. That day has not arrived, but as of 2007, there were more than 1 billion people who used the Internet, and more than 100 million websites. Radio frequency identification (RFID) chips that communicate wirelessly are embedded routinely in everyday products. Computers regulate the performance of automobiles and other devices and track, transmit, and recount product history, performance, and anomalies to networks of automotive dealers and others. Sensors can be found in seismically active areas or in tornados tracking the intensity, direction, and forces associated with atmospheric, oceanic, or seismic movement. Intelligent and communicating devices can be found in the backpacks or bracelets that accompany Japanese children throughout their day, and they are now frequently implanted in our pets.
Technology has become standardized, personalized, miniaturized, economical, ubiquitous, and even friendly. Connection to the Internet is becoming persistent. Many people now routinely carry a multiplicity of devices whose power far outstrips that of ENIAC or Manchester’s Baby. The evolution of context awareness, user interfaces (such as virtual worlds), and natural language processing will continue to erode the boundaries that separate our face-to-face presence from our presence in virtual spaces.
Finally, this period has seen the maturation of virtualization technology. Virtualization refers to the abstraction of computing resources and makes it possible to do things such as abstracting storage from networked storage devices, or hosting computer applications on alien hardware or software platforms. Virtualization makes it possible to optimize underused computing resources independent of their location. In the ideal, virtualization suggests the possibility of unifying a college or university’s far-flung collection of networked devices for the purposes of managing costs, conserving power consumption, applying security, promoting sound information practices, and enforcing institutional policies. These same capabilities, of course, will make it possible to reconsider the campus altogether as the locus of enterprise computing. Table 2 summarizes some of the key shifts in computing and communications that have occurred in this period.
| Table 2. Key Shifts in Computing and Communications | |
| FROM | TO |
| Computers are rare and expensive. | Computers are affordable and are nearly everywhere. |
| Computers and computing are isolated. | Computers are connected. |
| Computers are stationary. | Computers are mobile. |
| Networked computing is an enterprise-scale professional endeavor. | Networked computing is a widely held capability and activity that spans consumers of all ages and a wide range of personal and professional roles. |
| Computing, network, and data storage capacity are fixed and must be managed for growth. | Computing, network, and data storage capacity can be virtualized, shared, and increased or decreased on demand. |
| Information systems, resources, and services are organized, assembled, mediated by the enterprise. | Information systems, resources, and services can be organized, assembled, mediated anywhere and by anyone on the network. |
| Networked information resources are scarce. | Networked information resources are abundant. |
| Finding networked information requires end-user education and skills. | Finding network information is relatively natural and easy. |
| Standards are evolving and impede progress. | Many key standards are in place and standard-setting processes have themselves become standardized. |
| The physical form of information mediates access to information. | Policy and law mediate access to information. |
A Confusing Cusp
So what can we conclude is happening? Somewhere between the stable, yet adaptable history of the tower and the boisterous and disruptive history of information technology, things have become unclear. Why has it become increasingly difficult to predict the channels that IT may cut in higher education? Is IT a tool that we control or will information and communications technologies profoundly influence and perhaps deeply disrupt higher education?18 Have things become so murky that we can only predict the present or have we arrived at a moment of history when “change is so speeded up that we begin to see the present only when it is already disappearing”?19
We are in a time of emergence when the best advice is to observe and to be sensitive to areas from which change is emerging. Periods of emergence are characterized by hype, hope, rational and irrational exuberance, uncertainty, promises, panaceas, hyperbole, fear, risks, and opportunities.
This volume was intended to define the perimeters of this fluid and uncertain period. Not only is the rate of change accelerating, but the form that change is assuming is becoming indistinct. The form that change is assuming is that of a cloud. Cloudiness denotes heterogeneity, dynamism, shape shifting, indistinctness, and the capacity for expansion and reorganization. Cloudiness also denotes confusion and lack of clarity. We are at change’s borders and we cannot fully envision the territory that lies ahead. We are at a cusp—an interregnum that separates innovation and socialization. We are making the leap from one innovation curve to another. We are changing regimes without really comprehending the new regime. We are letting go of a known and trusted toehold in favor of an uncertain one.
Our uncertainty makes sense. Technological changes typically outpace people’s ability to socialize those changes. While innovations like the steam engine replaced the power of humans, animals, wind, or water with mechanical power in the 18th century, the reorganization of work itself changed very slowly and over a long period of time. Indeed, it was not until the 1918 opening of Henry Ford’s Rouge River plant—the cathedral for the Industrial Revolution—that industrial work finally and fully embraced the capacity for change presented by the technologies of the industrial age. The gap between innovation and full realization took more than two centuries to disappear.
This interregnum, too, is unique. First, clouds do not get clearer as you approach them. Second, the acceleration caused in fact by our interconnectedness means that this interregnum will not take 200 years to play out. The socialization of IT is a drama being enacted simultaneously by 1 billion interconnected people, many of whom are adapting to change and assimilating new behaviors in real time, all the time. Third, we are becoming cloudy. Grant McCracken argues that like clouds, we are “an aggregation of interests, connections, and contacts, tagged in several ways, linked in all directions, changing in real time.” This characterization of the self, groups, networks, and ideas stands in stark relief to Clifford Geertz’s concept of Western man as a “bounded unique, more or less integrated … dynamic center of awareness, emotion, judgment and action organized into a distinctive whole.” At its most philosophical, this particular cusp causes us to ask the most uncomfortable questions about the nature of enterprise, the nature of work, the nature of knowledge and ideas, and the nature of ourselves.20
The end of the middle, indeed.
Disruptions at the Cusp
So what is clear? It is clear that the history of higher education is one of persistence and adaptability. It is increasingly clear that core competency of universities “is not transferring knowledge, but developing it [through] intricate and robust networks and communities.”21
It is reasonable to conclude that higher education’s history is a history both of rising importance and accessibility and of continuity in instructional method. This history is partly defined by the tension between the academy’s costly craft-based instructional preference—defined as “quality”—and the drive to provide affordable higher education to more and more people. Increasing access to higher education has for most come with increasing costs and at the expense of personalized instruction. Few educators can deliver personalized instruction affordably on a large scale, without endowments or other subsidies. The history of higher education is also a history of increasing openness. From the time of locked and guarded scriptoria and of chained books to the proliferation today of open repositories, open content, open source software, and open inquiry, the vector of change has been easy to discern.
The history of information technology is similarly a history that can be summarized by the increasing availability of IT, of IT-enabled services, and of information itself. Unlike higher education, the history of IT is one of increasing accessibility with increasing affordability and increasing personalization. This is due largely to the breathtaking effects of Moore’s law, to near ubiquitous network access, and to the adoption of standards. And with IT, investment in personalization means ultimately that success is defined by making operations and learning so transparent and easy as to eliminate the need for human intervention. Most higher education offerings are predicated on the desirability of human intervention.
While so-called cloud computing remains an emergent concept and development and thus is subject to hype, definitional disputes, and inevitable fits and starts, it is clear that (1) open information content, software, and services, (2) service orientation and delivery, (3) server and storage virtualization, and (4) standardization of computing across the Internet are leading to what some describe as the democratization and industrialization of IT.22
Philosophizing about the cloud and the possible dematerialization of things can lead one to end-of-time ideas about the “big switch,” the “digital enterprise,” and the “end of corporate computing”23 or to incapacitating confusion and inaction. This volume and essay are in fact organized to accent an important portion of the trends so that the practitioner can engage the institution in setting a broad agenda for action in the coming years. While the prospect of “end-of-the-middle” possibilities is quite real, there are more fascinating and more positive questions to be asked. In particular, can enabling our IT infrastructures for industrial-scale computing make it possible to defeat the historical tension between access to and personalization of education? Can we extend the footprint of our existing colleges and universities in ways that take advantage of scale economics, while maximizing the degrees of operating freedom enjoyed by our students, faculty, operating units, international affiliates, and so forth? In short, is mass personalization of higher education possible?
To answer these questions, we need to understand the nature of the disruptions that are likely to occur in the future. University of Virginia Vice President James Hilton makes a compelling case that “four disruptive forces are bearing down on higher education at this very moment: unbundling; demand-pull; ubiquitous access; and the rise of the pure property view of ideas.”24
Unbundling
Unbundling, or disintermediation, makes it possible for the consumer to acquire only the blurb rather than the book, the cut rather than the album, or perhaps the course rather than the academic program. It is now possible for traditional colleges and universities to offer coursework in learning centers, on campuses, online, and in a variety of hybrid forms. It is also increasingly possible for new colleges and universities to do the same, and for institutions to sell unbundled educational offerings across traditional higher education jurisdictions. It is also possible for other “knowledge” and expertise businesses, such as The New York Times, to rebundle their human and information resources and reinvent themselves as educational enterprises, and for others to explore reconstructing the educational delivery model altogether. Just as one can unbundle a course from a catalog, one can unbundle course delivery from classrooms, and so forth.
Unbundling cuts both ways. Savvy education providers with strong brands will be able to enlarge their institutional footprint by organizing education and other institutional services for delivery to new students, customers, patrons, and fans. For others, the virtualization of services and the evolution of cloud-based services will likely add new competition for the mix. For still others, the availability of virtualized services will make it possible to rebundle elements of the educational infrastructure (tutors, library materials, assessments, and so forth) in ways that are experientially rich while being scalable and enjoying very different economics from their place-based alternatives. In an era of increasing concern about an institution’s carbon footprint and energy costs, such virtualized service offerings may become especially appealing.
Hilton also reveals another aspect of unbundling—the unbundling and repackaging in the cloud that is embodied in the creed of ripping, mixing, and burning. Not only does the cloud enable the unbundling of higher education’s service offerings, it facilitates a world of “mashed up” IT applications, expression, ideas, and scholarship. Ideas move through the cloud at the speed of light. They are mashed together with other ideas, commented on, transmuted, embedded, enlivened, debased as they circle the globe. Unbundling, in this regard, in its most positive light, presents the academic with unprecedented access to other interested scholars—and amateurs. In astronomy, for example, this is making it possible for theoretical astrophysicists to accelerate the pace of observational confirmation (or disconfirmation) by tapping into networks of amateurs. Every home can become part of a global observatory, meteorological data collection station, and so forth. In this same positive light, harnessing the talent and effort of the crowd can reduce the amount of time taken on an academic task and can simultaneously increase an institution’s fee base while “maintaining links to the sort of practical expertise they often lack.”25
Unbundling can disrupt an institution and industry so as to cause fragmentation. The potential to unbundle, for example, the offerings of the mainstream media has resulted in the likely permanent fragmentation of the mediascape. On one hand, citizen journalism is putting more news into more hands faster and faster without the overlay of corporate or governmental editorial policy. On the other hand, advances in technology have helped “turn each of us into producers, distributors, and editors of our own media diet.”26 While this is liberating, Farhad Manjoo reminds us that “while new technology eases connections between people, it also paradoxically facilitates a closeted view of the world, keeping us coiled tightly with those who share our ideas. In a world that lacks real gatekeepers and authority, and in which digital manipulation is so effortless, spin, conspiracy theories, myths, and outright lies may get the better of many of us.”27 The vision of higher education splitting into niches of scholars, students, amateurs, and others who are united by common biases and preexisting beliefs is an unnerving one. However this aspect of unbundling plays out, it is likely that unbundling and rebundling words from their authors represents what Professor Chris Dede calls “a seismic shift in epistemology.”28
More narrowly, unbundling has real disruptive consequences for those of us who manage the institution’s information, information services, and information resources. A great deal of the scholarly information resources of the planet are being digitized at the same time that unprecedented investments are being made in search engineering. These forces are unbundling the collection from the library. Similarly, markets for delivering core aspects of the IT infrastructure—compute cycles and data storage—are emerging and will likely mature quickly. Virtualized IT infrastructure and application services, such as mail, make it possible to increase or decrease the institution’s IT consumption on demand, take better advantage of scale, and in some cases take advantage of providers’ access to renewable energy sources. Commercially provided cloud services, in the long run, are also likely to feature better security and improved business availability. It is increasingly likely over the long term that core higher education processes will be available as cloud services.
Demand-Pull
If unbundling is a phenomenon that speaks to what producers do (or what happens to them), then demand-pull relates to the capabilities, preferences, and behaviors of consumers in a cloudy world. Just as the cloud is making it possible for producers to deconstruct and re-source their services, it is making it possible for consumers to assemble their world. One student put it this way: “I don’t look at it as ‘getting on the Internet.’ The Internet is a part of life. It is a lifestyle.” Part of that lifestyle includes RSS feeds, social networks, portals, and other tools that make it possible for people to configure their social and informational worlds in cyberspace precisely to suit their needs and tastes.
In the context of higher education generally, the emergence of a robust tool set for configuring our world is enormously powerful and beneficial. We are able to consume more relevant information, faster, and share insights within purposeful communities more effectively than ever before. Because developing and transferring knowledge within communities is a part of our educational mission, an infrastructure that empowers us to configure and contextualize our world levers this mission. However, as with unbundling, the sword cuts both ways. Our students and other constituents, too, are using tools to arrange their worlds. Higher education, like many industries, is organized today in a producercentric fashion. We are supply-push–based institutions. We don’t offer a course on the history of feudal Japan, but we have a raft of wonderful Byzantine history courses you can take. In an unbundled cloud in which the consumer has been fully empowered, we run the risk that students will lose confidence in our ability to construct curricula that meet their needs. Like their medieval counterparts, students will have the easy ability to use their social or scholarly networks to source the academic programming they want. In the extreme, faculty free agents—like the itinerant scholars before 1100—may find interesting niche opportunities among such bands of students. This massive customization or personalization of an education is no different from how students today organize and consume their news or organize their philanthropic or social agendas and communities.
Another interesting aspect of this potential disruption is the long-tail phenomenon. Chris Anderson argues that “the future of business is selling less of more. Infinite choice and lower costs to connect supply and demand is changing the nature of the market and will transform entire industries. Growth is in the long tail.”29 The long tail of demand may—in concert with an institution’s course delivery system—provide ways for comprehensive universities to continue to offer instruction in rare and exotic fields while expanding student choice, either independently or at smaller institutions. The long tail of demand may express itself in efforts by smaller colleges to enlarge their footprints by importing parts of an expanded curriculum. Or students may simply customize their courses of instructions themselves.
For the college or university administrator and IT leader, the move to a demand-pull economy is similarly disruptive. Faculty will be presented with the opportunity to use cloud-based services to manage their grant activity and to organize a personalized e-research infrastructure in the cloud. Faculty will also be able to use their institutional platforms to launch extramural consulting, teaching, and other ventures.
When the forces of unbundling and demand-pull combine, the results are easy to visualize. The growing availability of low-cost, easy-to-use devices and cloud services makes it possible for today’s student or new faculty member to arrive on campus with an intelligent phone, portable digital music player, laptop computer, router, social networks, e-mail accounts, network data storage, RSS reader, and perhaps open source office productivity tools and web development environment. The lament of tomorrow’s IT provider could be: “There go my customers. And I must hurry to follow them. For I am their provider.”30 As the explosion of content continues along with the increasing maturity and availability of web-based academic services and applications, tomorrow’s students will arrive on campus with their own IT architectures and service arrangements. These students—and tomorrow’s faculty—will have little use for or patience with college or university offerings that underperform or force them to lose precious connections to people and processes that they have accumulated since childhood.
Ubiquitous Access
The first 50 years of the IT revolution were preparatory. In essence, the race to miniaturize computers, put them on desktops, make them portable, and connect them to networks met the preconditions for a networked information economy. The invention of the World Wide Web and the widespread adoption of search engines—and in particular Google—have made the Internet a transformative medium. As James Hilton puts it: “We are on the cusp of a world in which everyone will have access not only to online information but also to information that traditionally was accessible only by going into a library … . Any information that one could desire will be but a click away.”31
The importance of having more than 1 billion people and nearly all published information online cannot be overstated. Such milestones suggest the arrival at tipping points—in the roles played by traditional libraries and in the roles played by academics. In the near term, this is all liberating. No longer will information be rationed by the availability or scarcity of books, serials, government publications, and so forth. No longer will students and other researchers be constrained by search techniques that are confined to the small number of subject descriptors supplied long ago by catalogers.
The capacity to create or follow hypertext links creates opportunities to follow, develop, or abandon research trails at a rate that could not be imagined 10 years ago. Google, for example, is working with 20 major research university libraries worldwide to make their collections available over the Internet. Columbia University Librarian James Neal argues that “[Columbia’s] participation in the Google Book Search Library Project will add significantly to the extensive digital resources the Libraries already deliver. It will enable the Libraries to make available more significant portions of its extraordinary archival and special collections to scholars and researchers worldwide in ways that will ultimately change the nature of scholarship.”32
The nature of scholarship has changed and indeed must change in light of ubiquitous access. The emergence of the networked information economy has made information and knowledge central to human development and progress. The premium on information and knowledge—and on processes for creating and socializing this information and knowledge—carries with it the potential for colleges and universities to occupy places of increasing centrality. These vectors of change also create opportunities for others. As Hilton concludes, the function that colleges and universities have played as gateways to information will be gone: “If higher education remains synonymous with access to information in the eyes of the public, then it has a huge problem. There are many more efficient ways to get information than attending classes for four years.”33
The Rise of the Pure Property View of Ideas
The very rich IT infrastructure that we have created has made it possible to deliver everything in digital form and thereby to code it, tag it, watermark it, track it, and extract rents from it. The long-standing calculus of copyright law and patent law—which strives to balance the limited rights of creators and inventors to enjoy compensation for their creative contributions and effort with the overarching public right and need to have, share, and develop ideas—is being revised in both directions.
On one hand, copyright and patent law “are moving aggressively in the direction of protecting owners and away from protecting access and learning. Even more important, our understanding of the nature of ideas is shifting.”34 Students are asking professors to sign nondisclosures to protect their rights to intellectual property in course assignments; the rights to alleged prior art obtained in open community discourse is at the heart of high-profile patent litigation and reexaminations; and so forth. The past few decades have witnessed the extension of copyright protection to all written works at the moment of their creation and this protection has been extended in duration.
At the same time a vigorous, if struggling, movement has arisen to liberate scholarly and other information from the strictures and constraints of copyright and patent law. Open source and community source software have become commonplace, if not clearly or comprehensively sustainable. Open courseware initiatives of varying intensity are under way at many colleges and universities. These efforts make available course content, instructional frameworks, syllabi, and in some cases textbooks and even limited access to instructors. These initiatives bear witness to three important observations. The first is that for some learners and some learning purposes, disembodied learning content that is well contextualized in a learning framework and supported by indicators of progress and self-administered assessments can be quite effective. The second is that some learners do not need mediation of course materials by experts, guides, and peers. The third observation is that giving away this wealth of material does not impoverish the donor. Indeed, the reputation enhancement alone of providing open course content suggests that these initiatives are net economic winners for their sponsors. These economics were understood in 1813 by Thomas Jefferson35 and more recently by John Perry Barlow. Barlow argues:
You take a piece of information and share it between two people and that same piece of information becomes more valuable, because it now has a context that automatically makes it more complex than it was before you shared it. It layers new forms of value onto itself with each iteration. You get a deeper understanding, a better strategy, a more finely tuned approach. This is a very different way of looking at the economy than the one we have been using, which is based on physical objects. Scarcity of physical items increases their value, which is not necessarily true of information. With information such as music or books, the better something is known, the more valuable it becomes. Most of the economic value now is coming out of the informational world, not the physical.36
And finally, consumers in many cases are taking matters into their own hands. The compelling and perhaps inexorable flow of information on the Internet is the free flow of information. Outside the civilized, if passionate, arguments for greater openness or more protection of rights, markets are operating. Network babies who have grown to adulthood accustomed to unimpeded movement across network environments are developing and socializing their own ideas and morality around intellectual property rights. Whether rights holders can educate or sanction young people into conformance with the pure property views of information or Net Gen citizens grow up to reflect their own ideas in the workplace and ballot box remains to be seen. In any case, it is not hyperbole to suggest that as digital delivery of protected textual becomes the norm, this issue will divide higher education as perhaps no other.
Toward a Cloudy Academy
Former Wellesley College President Diana Chapman Walsh and her commissioners at Wellesley College argue persuasively that colleges and universities operate increasingly in a fluid and uncertain environment. Higher education in the future will need to come to grips with globalization and will be subject to worldwide competition. Long-standing demographic trends are playing themselves out in ways that will reshape the world. The populations of many leading nations are expected to collapse in size within two or three decades, and much of the developed world will need to meet the demands of large numbers of older citizens.
The ascendance of knowledge work places a premium on education and presents the possibility of a new centrality and vitality in the role and place of the college and university in society. This possibility is also presented to other potential educators, and it is likely that the ongoing progress of virtualized services, web standards, open information, and other developments will make it increasingly possible to unbundle parts of the higher education mission and thus to invite new competitors and forms of competition. And despite our nearly ubiquitous access to each other and to an increasingly complete digital record of human activity, the threats of fragmentation and polarization are higher than ever before.
Walsh and her colleagues point out that “the Internet has provided everyone with a voice, and the cacophony of clashing worldviews and faith systems [that are] overlaid with political and social agendas … .”37 They also point out that another critical aspect of this uncertain environment is the climate of ferment in higher education, a growing view that “the system [of U.S. higher education] has serious enough deficiencies in access, quality, and costs as to raise concern about the nation’s long term prospects of sustaining its standard of living in a newly-competitive global economy.”38
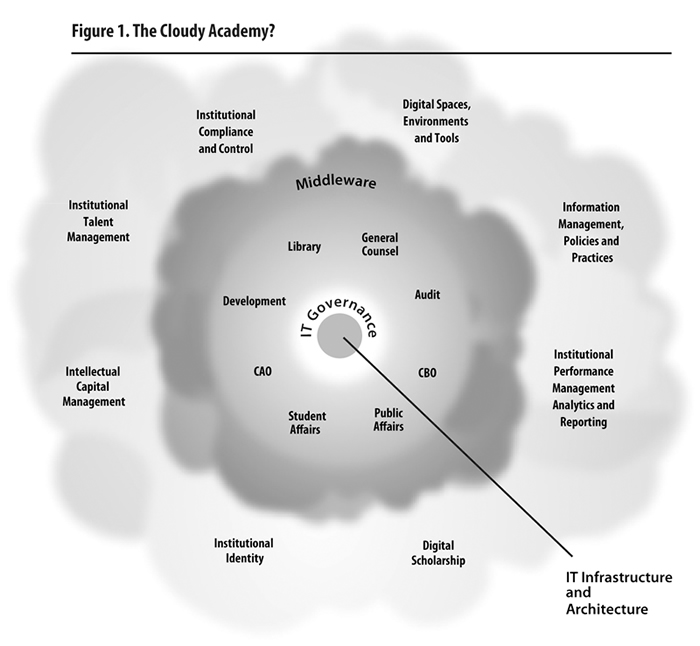
The emergence of new technological capabilities, of the disruptive socialization of these capabilities, and of this fluid and uncertain environment suggests a plan of action and a set of priorities for colleges and universities. In many ways, the emergence of the cloud presents yet another opportunity to visit what John Henry Newman called “the idea of a university.”39 This essay and this volume suggest an agenda for discussion, debate, and eventual decision as colleges and universities work toward a cloudy academy. This agenda for action is described in Figure 1.
Develop a Cloud Strategy
Whether or not the cloud metaphor is right, it is clear that the capacity to dial up IT infrastructure and to invoke services over the network is evolving. This evolution presents enormous opportunity and risk. We can leave our institution’s response to these new capabilities to chance, we can confine our planning to the IT organization, or we can engage our leadership in a discussion of near-term strategy. The strategic discussion about the evolution of virtualization, services orientation and delivery, open resources, web standards, and cloud computing is in fact a conversation about what constitutes the institution as an enterprise and about how the institution wishes to manifest its institutional presence in cyberspace. Embedded in this strategic conversation is the issue of the institution’s predispositions as a provider or consumer of network-based services and whether these predispositions are outward facing or inward facing. For example, the institution may choose—for this time—to be dominantly a consumer of services externally and to not “cloudify” its external services. At the same time, the central IT organization may opt to virtualize elements of the institutional IT environment on behalf of local campus units. Strategic alternatives range from doing nothing, to becoming an aggressive integrator of infrastructure and services from the cloud, to rationalizing IT resources internally, to enabling the institution to become a supplier of services in this evolving fashion. Each option, of course, suggests a different infrastructure and bears distinct investment and operating costs.
Focus on IT Governance
Every IT leader understands the importance of governance in higher education. The emergence of cloud computing and of the issues raised in this essay suggests the need to redouble our efforts in this arena. If the wellspring of higher education’s creative success and our organizational inefficiency is the empowerment of students and faculty in the academic enterprise, then the emergence of the cloud will amplify this empowerment. Just as PCs unleashed end-user creativity while proliferating copies and versions of the institutional record, and just as the emergence of the web and HTML have produced both a cornucopia of content and a multiplicity of front doors to our institutions, the next turn of the IT crank will make it possible for every member of our community to become her own IT provider. The potential both for unlocking human potential and for further fragmentation is profound. This potential will affect the institution’s presence and reputation in cyberspace, our social compact with our community, our business controls, costs, and risks, our ability to manage risk and to comply with regulatory requirements, our competitive posture, and other major issues.
These issues may first become visible to the IT leader, but they are not IT issues. Therefore, it is essential that institutions begin to allocate concerted and ongoing leadership attention to the questions and challenges raised by IT in the years to come. IT governance will continue to focus on the institution’s IT investment strategy and priorities but will increasingly focus on how the institution wishes to manifest itself online. Failure to govern will lead to accidental governance and to the future need to “rope in those clouds.” As one imagines, clouds are hard to rope!
Focus on Information Management, Practices, and Policy
This topic is pressing. It is deceptively labeled, since everything in the Internet is information! How an institution manages its virtual presence has become as important as how it manages its campus and physical presence. Increasingly, these issues are merging as laboratory access, library access, building access, and so forth become mediated by IT. The institution’s information system is increasingly the means by which the institution regulates the boundaries and conditions of its community, the rules of community engagement, and the boundaries, scope, and nature of that community’s access to scholarly resources. These are issues that are instantiated in and enforced by IT but, again, they are not IT issues. Who are the citizens of our institution? Do all citizens have full rights of citizenship? What authorities do different citizens have? Who determines these authorities? Do citizens of allied institutions have rights at our institution (and vice versa)? These are profound questions that are shaped in part by the regulatory environment but even more by decades or centuries of campus experience and policy making.
Ubiquitous access to people and resources through the network makes the institution’s information system the nexus of enforcement of these policies and practices. In many cases, this means that formal and informal practices must be made explicit. As new technologies make it possible to virtualize storage or to federate data, it will also become more critical for institutions to craft information management policies and strategies. Institutional information is increasingly subject to regulatory requirements related to access, privacy, confidentiality, discoverability, redactability, retention, disclosure, and so forth.
At the heart of the information policy issue is Professor Yochai Benkler’s concept of network permeability. Benkler argues that the way information and knowledge are made available can either limit or enlarge the ways people can create and express themselves.40 As well, institutions need to devise policies and practices to ensure the authenticity of official information and to preserve a record of the institution and its citizens for cultural and historical purposes.
Finally, the need to reshape information management, policies, and practices carries with it the need for institutions across higher education to rethink their revenue models. The revolution in open source computing is being fueled in part by competitive investments by some companies against the entrenched monopolies of others. Or it is motivated by a shift from product delivery to solutions. Open content strategies of search engineering organizations or social network operators also have an underlying revenue model—becoming the “library of the world” means attracting visits and therefore advertising; that is, attracting crowds attracts advertising revenues.
Higher education’s impulses toward openness are essential to diffuse knowledge, build community, and stimulate innovation. Openness, however, is not free, and therefore colleges and universities, like others, will need to develop, evaluate, and eventually deploy new strategies for recovering the costs of their investments in openness.
Focus on Key Technologies and Enterprise IT Architecture
While the technologies themselves may be the least complex of the issues associated with this transformation, they are not at all simple. The enterprise IT leader will be charged with organizing the infrastructure and human capabilities that will enforce the leadership’s views about the nature and privileges of the community. While it may be axiomatic that the IT leader must track and test virtualization technologies, web standards, cloud service offerings, and the like, the IT leader must also rethink enterprise IT architecture.
It is increasingly understood that validating identity and administering basic citizenship authorities can best be accomplished through middleware that spans institutional academic and business applications. It is also increasingly apparent that cross-cutting activities such as workflow management can also be rendered in middleware. Ongoing attention should be allocated to IT architecture and in particular to the tightness of how software functions are integrated and to which software operations can be abstracted from applications and embedded in middleware. IT leaders will have to become adept at identifying risk in systems and services they do not operate and will have to query cloud service providers deeply about policy choices that may be embedded in their service offerings. For example, some software capabilities may be enabled through information practices—such as mining and profiling student information—that are incompatible with laws such as FERPA.
Focus on Enterprise Compliance and Controls
The drive toward consumerization and unbundling is motivated by service. TripAdvisor, for example, has unbundled the hotel industry by aggregating room information and disconnecting this information from the hotels themselves. For the consumer, it is more pleasant to shop price and quality on one site than to call or surf dozens of hotel chains. Enterprise systems exist to facilitate service but also to mitigate risks, minimize costs, comply with regulations, safeguard privacy, protect reputations, and so forth. The drives toward unbundling and consumerization pose a real challenge to the enterprise, particularly to colleges and universities whose leaders are loath to impose strict limitations on a highly creative (and possibly tenured!) workforce.
Be warned: even the very idea of audit trail becomes difficult to understand in the context of software-as-a-service and cloud computing. The general counsel, auditor, business officer, and CIO, along with academic leaders, must work together to determine how much authority individuals and subunits have in the cloud. Just as institutions in the past have regulated purchasing activity, prequalified vendors, or injected CIO review into large-scale IT procurements, controls of some sort will be needed to make sure that what people can do in the cloud is consistent with what the institution wants them to do. This is very tricky. Colleges and universities have been embarrassed by data spills resulting from the theft of unauthorized copies of digital student or patient records. Imagine the fallout from news of institutional data loss, misuse, or leaks from third-party custodians whose very existence was unknown to institutional officials. Cloud services will not be limited to infrastructure and in time it will be relatively easy for well intended campus citizens to configure financial transactions and so forth.
The need for compliance and control is often misunderstood in the academy. Achieving control requires oversight, and in the context of networked information oversight is often achieved by filtering, monitoring, alerts, restrictions, and sanctions—activities that are unpopular in the academic enterprise. Nevertheless, strategic choices will need to be made regarding the institution’s approach to compliance and control. In general, colleges and universities will have to choose control systems that constrain employee action automatically (dollar limitations, preauthorizations, vendor lists, and so forth) or control systems that maximize employee freedoms but accomplish control through dollar limits (campus cards) or through monitoring and posttransaction sanctions.
Taking increased advantage of cloud services will be neither easy nor without risk. While cloud computing promises to eliminate software upgrade cycles, free us from vendor lock-in, and so forth, this style of organizing IT, too, will be very hard. Invoking services from the cloud is unlikely to ever be analogous to plugging into the wall for electricity.
On February 15, 2008, Amazon’s Simple Storage System suffered a massive outage. In a separate incident, thousands of early users of Apple’s MobileMe mail synchronization and backup utility were left unable to access their mail, and some witnessed the permanent loss of substantial amounts of mail. In a third contemporaneous incident, an online storage service called The Linkup shut down on August 8, 2008, after losing unspecified amounts of customer data. Company responses to all of these failures were reported in the press as being “substandard.”41
It will be wise to remember that any service will always have points of failure and that institutions that depend on hosted services must take care with language about risk levels in their contracts. Agreements will also need to ensure that third parties implement reasonable safeguards when they process, store, use, or transmit institutional assets. Vendor agreements will need to ensure vendor compliance with Sarbanes-Oxley, FERPA, HIPAA, and other key regulations, as well as with institutional policy on confidentiality and security in electronic communications. Colleges and universities will want to ensure that third parties do not monitor the contents of electronic communications except to ensure the proper functioning and security of electronic communications. Security incidents, losses of data, and other issues must be handled in ways that meet the institution’s policy and regulatory requirements, and contracting institutions should review the cloud suppliers’ professional guidance (SAS 70 Audit Report) that documents and attests to the adequacy of the internal controls for the service being contracted. And, of course, issues related to indemnification and insurance need to be specified. This is not just like electricity.42
Manage the Institution’s Online Presence
Since the early days of personal computing and the early days of the web, college and university leaders have realized that the willy-nilly proliferation of PCs and of institutional web pages was suboptimal from an investment viewpoint and presented the world with a fragmented and perhaps wrongheaded impression of the institution. The realization of the networked information economy suggests that over time, an organization’s presence online will assume greater and greater gravitas with consumers, regulators, accreditors, and others. This rising gravitas in concert with the unbundling tendencies inherent in the evolution of the networked information economy suggests the need to redouble efforts and investments to nurture the institution’s reputation in cyberspace. Creating and enforcing standards and guidelines for subunits regarding the use of the college or university name, its trademarks, message, and so forth will be essential, as will inventorying and monitoring the presence of institutional subunits and that of their partners in cyberspace. The reputations of enterprises in general will rise and fall increasingly as a result of actions, images, and impressions made in cyberspace. Colleges and universities and their faculty—like public officials, corporate executives, and movie stars—will need to monitor blog sites, wikis, social networks, faculty rating sites, newsgroups, and other social sites to inform efforts to maintain and elevate the institution’s reputation. This will become even more the case as colleges and universities move to immersive environments. As these environments become compelling and popular, their impact on institutional reputation will become inseparable from that of the physical campus.
Manage Digital Spaces, Environments, and Tools
As just mentioned, virtual and immersive college and university environments such as Second Life will deeply influence the image and reputation of the institution. They will also become places of serious academic work and commerce and therefore will demand the same quality attention that is devoted to physical campus master planning, design, architecture, and construction. Already a great many students and faculty interact in online collaborative environments. Major research collaborations take place in academic teams whose members may never have met face to face. Such environments must be designed thoughtfully to both stimulate sound academic practices and safeguard research results, as well as to reinforce the presence of the institution in positive ways. The unbundling capacity of new cloud capabilities will make it possible for academics to assemble just-in-time collaborative environments and to assemble an infrastructure and open source tools that might be needed to facilitate a learning encounter or research effort. College and university leaders should understand that to the extent that assembling such environments is easy and effective, others will assemble them and use them to potentially draw away increasingly talented faculty. Increasingly, unaffiliated research institutes are attracting away political scientists and other social scientists. Indeed, improved network capacity is now making it possible for scientists in unaffiliated organizations such as the Space Science Institute to conduct world-class research from home or otherwise away from colleges and universities. This trend represents another form of unbundling and can be countered in part by methodical and serious institutional investment in digital learning and research environments and tools.
Focus on Scholarly Literacy
Ubiquitous access has disrupted the social landscape of higher education in unexpected ways. Persistent networked access to countless people and to mountains of digital resources, according to Professor Yochai Benkler, go “to the very foundations of how liberal markets and liberal democracies have co-evolved for almost two centuries.”43 In this new environment, knowledge production has become an increasingly social activity. Ideas about authorship, provenance, plagiarism, collaboration, and ownership are all under experimentation in the wake of information technologies that make it possible to rip, mix, and burn. Unlike information in print, online digital information can be manipulated, extrapolated, extended, connected, hyperlinked, and mashed up. This new freedom “holds great practical promise: as a dimension of individual freedom; as a platform for better democratic participation; as a medium to foster a more critical and self-reflective culture; and, in an increasingly information-dependent global economy, as a mechanism to achieve improvements in human development everywhere.”44
This new freedom also challenges many of our traditional ideas about scholarly quality, method, and literacy. Debates simmer about the usability of Wikipedia as a scholarly resource because of its ephemeral nature and because the academic bona fides of its contributors cannot easily be vetted. Mashups obscure our understanding of authorship, and so forth. Seasoned academics will need to debate and ultimately shape a new understanding of scholarly method in light of these evolving practices, and students will need to be taught how to sift and evaluate evidence in the context of networked information.
Focus on the Institution’s Performance Management System and Analytics
Colleges and universities operate today in an overall period of educational ferment. Students and their parents describe feeling trapped between pressures to gain higher education bona fides for the workplace and the declining affordability of postsecondary education. This squeeze plays out in a number of ways. As the cost of collegiate education rises and as governments break with their long-standing commitments to underwriting this cost as a public good, students and parents have increasingly come to view the college or university offering as a consumer good. The enlightened consumer is less likely to accept academic offerings because such offerings are purported to be “for their own good.” Today’s students and their parents will pressure colleges and universities to create safe and fulfilling environments for study and personal growth, to foster their admission prospects with graduate schools, and to offer curricula that contribute to students’ long-term earning prospects. The continually rising costs of collegiate education are also conspiring to focus parents’ and regulators’ attention on perceived value, rankings, and other methods of assessing the comparative performance of colleges and universities.
This political ferment and a host of structural factors—such as demographic change—are conspiring to make the management and reporting of institutional performance a matter of substantive and political concern. The development of meaningful metrics, and the careful mining, analysis, presentation, and reporting of performance information in ways that both guide the institution and convey intentions and achievements to stakeholders, is hard in the context of any set of information systems. Accomplishing these objectives when information may reside in the cloud or on infrastructures hosted by others will be even harder. In the years ahead, the institution’s performance management system may become one of the defining elements of the enterprise. Thinking through what a distributed performance management system might look like should be a part of the action agenda for today’s leaders in higher education.
Focus on Managing Talent and Intellectual Property
Colleges and universities, as mentioned earlier, are purposeful communities designed chiefly to develop and disseminate new knowledge. We accomplish these purposes in complex but largely social ways. Former Harvard University President James Bryant Conant perhaps said best how this is done: “pick men (sic) of genius, back them heavily, and leave them to direct themselves.”45 Three background forces are evident: (1) within the next decade, more than half the professoriate and staff in higher education will retire; (2) emerging nations will meet an increasing amount of their citizens’ educational needs locally; and (3) all nations will seek to keep talented people within their homelands, and many will engage in a global hunt for talented people.
Colleges and universities in the West have long operated in an environment of abundant talent. In many areas of academic endeavor—particularly the humanities—the supply of talented instructors has far exceeded our ability to employ them. This is, of course, not true across the academic board. It seems clear that in an environment of extreme competition for talent, colleges and universities will be well advised to consider how the emergence of the cloud may make it possible to compete and win talented students and faculty. Many of our institutions are systematic, if antiquated, regarding the competition for students of talent, but nearly all are ad hoc and antiquated when it comes to developing the institutional workforce of the future. Commercial firms understand the prospects of a looming talent war and are organizing their federations, partnerships, relationships, databases, alert systems, and relationship management infrastructures to discover, uncover, source, evaluate, cultivate, develop, and retain people of talent—across the globe. If President Conant is right, higher education’s stakes in talent management are very high, and the current informal and cottage industry approaches must likely give way. Talent development is an inherently “cloudy” activity since much of the activity and information lies outside the perimeter of the institution’s borders. It is perhaps an enticing area for institutions to engage in early experimentation.
Consistent with President Conant’s exhortation, colleges and universities must focus concerted effort on managing their intellectual property. The postscript to his advice, of course, is: and we do this so these bright people will produce great stuff! How institutions manage the great stuff they collect and create will become increasingly complex and consequential in the future. Today, the motion picture industry and the recording industry are asserting unprecedented hegemony over film and musical content. In the near future, the publishing industry will assert the same hegemony over text and still images. Higher education’s historic rights of fair use will come under increased scrutiny and challenge as it becomes technically easier to monitor digital content flows at the level of the snippet or the individual image. How an institution manages these issues—as both a producer and consumer of digital information—will deeply influence that institution’s implicit compact with students and faculty, its costs, its capacity to innovate, and the nature and depth of its external relationships.
Summary
During the past thousand years, Western colleges and universities have pursued a mission of instruction, research, and services. The process of research has changed dramatically while instruction continues to rely on personalized interactions among students, journeymen, and masters. In higher education, increasing demand for access abuts a delivery system that depends on personalized instruction, making it difficult to contain costs.
In the past 60 years, a revolution in computing and communications has occurred. Computers have become faster, smaller, and cheaper and intelligence is now embedded widely in things of all kinds. Computers have become connected and today more than 1 billion people regularly access the Internet. New technologies and standards are making it possible to virtualize computing power, network bandwidth, data storage, IT security, and a host of services and processes.
The revolution in IT is making possible the emergence of a networked information economy, one that is simultaneously centered on information and on the existence of cheap computation and persistent connection to a global network. Ubiquitous access to people and between people and information resources and services is profoundly disrupting institutions of all sorts. These disruptions include the massive empowerment of the individual consumer to do things and the ability of large-scale service and infrastructure providers to sell interoperable personal and enterprise capabilities over the network. These disruptions in turn are leading to the evolution of new creative relationships among people, new and beneficial cost structures for businesses, the unbundling of services, and the globalization of talent and economic prosperity. They are also contributing to increased fragmentation, balkanization, and politicization of discourse and to the rise of new industries and approaches that will threaten traditional ones. It is a fluid and uncertain environment.
Colleges and universities are institutions with long-standing reputations. In the United States and in much of the West, colleges and universities are intimately associated with the campuses. They bundle their academic programs, selling degree programs and certificates in preference to selling individual courses. This preference reflects both long-standing beliefs about education and a desire to insulate themselves from the full effects of economic markets. Bundling courses makes it possible for popular courses to subsidize less popular programs. Society in general and students in particular benefit from this academic diversity.
The emerging networked information economy creates unprecedented opportunities for colleges and universities to rationalize their highly distributed IT resources and to extend their institutional footprint. This economy also creates these opportunities for new producers, including providers of related services such as newspapers, media conglomerates, publishers, and others. For IT, the twin trends of consumerization and industrialization of IT raise concerns about the “end of the middle,” that is, the disappearance of the enterprise role in managing and mediating information technology, resources, and services. Such concerns are articulated in a literature with titles such as Does IT Matter?, The End of Corporate Computing, and The Big Switch. It is important to note that the college and university enterprise itself is a “middleman” interposed between the teacher and learner. Consumerization and the industrialization of IT—in extremis—could undermine some institutions as well.
The twin forces of consumerization and industrialization of IT represent neither the end of enterprise IT nor the end of the enterprise in higher education, but an opportunity for colleges and universities to consider new ways of increasing access while remaining personal and affordable. These forces are making it possible to realize MIT President Emeritus Charles Vest’s vision of the metauniversity, a “transcendent, accessible, empowering, dynamic, communally constructed framework of open materials and platforms on which much of higher education worldwide can be constructed or enhanced.”46 Virtualizing IT infrastructure and services—over time—will benefit from economies of scale and of standardization, enhanced power consumption, improved security, and so forth. Improved resource sharing techniques will also optimize the use of these resources, reducing again their cost. The ability to increase computing, storage, and network bandwidth on demand will make it possible for institutions to contemplate new growth options by substituting large, fixed capital costs in land acquisition and development with smaller variable costs in digital delivery of services.
The tower’s place among the clouds will be a complex one. Rather than disappearing, the role of enterprise IT will expand. IT will become increasingly an activity that is strategic to the institution, and its conduct will depend on the effective inclusion of key leaders of the institution.
- An institution’s effectiveness in the networked information economy in general and on the cloud in particular will depend on IT governance and on institutional strategy. It will depend, too, on a fabric of rules that will shape how people flow in and out of the campus community and how access to the institution’s information, tools, services, and other resources is mediated. Most important in this matrix of decisions, institutions will need to develop points of view about the openness of their research processes, course content, publications, software, instruments, and information resources.
- Colleges and universities will need to understand what data and information are the responsibility of the enterprise. We will also need to grapple with how information can be stored and protected—perhaps in perpetuity—either on enterprise storage devices or “in the cloud.” We will need to understand how an institution’s digital holdings influence its reputation in the way that print library collections have.
- We will also need to develop shared views about the nature of the evolving epistemology and how concepts such as crowd sharing, mashups, and wikis interact with traditional scholarly methods and beliefs. Our disciplinary leaders will need to begin to articulate a new scholarly literacy to enable students to understand the authorship, credibility, valence, and provenance of the digital evidence they use. Academic leaders will need to spread changing norms and values among their campus colleagues.
- Maintaining and enhancing the institution’s identity in cyberspace will demand more attention than ever. As new technologies promote unbundling, there is a risk that many institutional reputations will be leveled. Thoughtful attention to an institution’s presence in cyberspace will be important as well as attention to the use of its brand and trademarks.
- Increasingly, issues of institutional compliance and control will be mediated through the information system and, by some, through partners in the cloud. New skills in contract administration will be critical, and issues such as indemnification for service interruptions and data losses will be very problematic.
- Colleges and universities will need to manage the look, feel, and overall characteristics of virtual and online environments with as much deliberation and care as we manage physical space. This will become particularly true as immersive environments such as Second Life become platforms for the delivery of key institutional offerings and for academic collaboration.
- If and as enterprise activities move to the cloud, advance thought needs to be given to the institution’s performance management systems and to how it wishes to use data and information to support decision making, student success, financial performance, and accountability.
- Colleges and universities are organizations that depend on attracting, developing, and organizing human talent for the purposes of creating and disseminating intellectual capital. In the environment described we will need to pay close attention to how IT extends the reach of the institution through the cloud and how institutional property is to be developed, disseminated, commercialized, and put to use.
Higher education will likely operate in a continually fluid and uncertain environment. Amidst this fluidity it seems clear that being digital is indeed a lifestyle and that all members of the academic community will engage the networked information economy. It is also clear that computers and networks will continue to become cheaper, better, and faster. Digital information will become cheaper to store, more plentiful, and easier to find. It is not clear whether information will become more openly accessible or if rights owners will demand economic rents on smaller and smaller snippets for longer periods of time.
What is certain is that the trend toward consumerization will continue. Colleges and universities loath to take a stand may discover that they have arrived at accidental cloudiness. Inaction may not be an option if institutions wish to regulate their IT, service, control, and information environments at all. What is also certain is that the shift to cloud computing will be hard—a “brutal slog” as one reporter calls it.47 For some colleges and universities, engagement in the evolving networked information economy will—at the enterprise level—remain a choice. Well endowed and highly selective institutions will be able to choose whether, how, when, and for what reason they become cloudy suppliers or consumers. Large and highly decentralized universities will likely adopt cloud strategies internally to rationalize IT resources and will likely become selective suppliers and consumers of cloud services. Institutions that are more resource constrained will, as always, need to be more strategic about alternatives.
The end of the middle? Not likely. Exploiting the opportunity of so-called industrial computing will demand care, time, thought, and resources. The move to bring the tower to the cloud before the cloud grows to envelop the tower will engage nearly every institutional leader and challenge every institutional policy. The gathering cloud creates an unprecedented opportunity for the prepared. We are talking no longer about managing IT; we are managing the enterprise.
Endnotes
- Plato, “Phaedrus,” 67–71, Socrates to Phaedrus, The Dialogues of Plato.
- At the same time (830 AD), the House of Wisdom in Baghdad was the first institution of higher learning in the Islamic world. This institution functioned as an academy and was a center for translation and an important library and observatory. By the 8th century BC, Chinese higher education was already mature and institutionalized and more than 3,000 students prepared for careers in the Chinese imperial bureaucracy at the Great Academy. Unlike their medieval or Renaissance counterparts, which encouraged disputation in the learning process, Chinese education focused on students’ familiarity with “a general ethical outlook, and body of knowledge, not with [the] growth of knowledge …” See John Merson, The Genius That Was China: East and West in the Making of the Modern World (New York: Overlook Press, 1990), 86.
- See W. Warren Wagar, H. G. Wells: Traversing Time (Middletown, CT: Wesleyan University Press, 2004), 162.
- John Seely Brown and Paul Duguid, The Social Life of Information (Cambridge, MA: Harvard University Press, 2000), 11.
- Ibid.
- Diana Chapman Walsh, Envisioning the Future: Reflections from the 2015 Commission. Final Report (Wellesley, MA: Wellesley College, 2007), [http://www.wellesley.edu/PublicAffairs/President/DCW/Announcements/2015synopsis.pdf].
- Thomas Jefferson, letter to Tench Coxe, 1795. In Jeffersonian fashion, Supreme Court Justice Potter Stewart argued that “in the absence of governmental checks and balances present in other areas of our national life, the only effective restraint upon executive policy and power … may lie in an enlightened citizenry,” in New York Times v. United States, 403 U.S. 713.
- Rudolf Stichweh argues that “in its ultimate realization, higher education at a research university takes place as participation of the student in the research process,” in Thomas Pfeffer, Virtualization of Research Universities: Raising the Right Questions to Address Key Functions of the Institution, Paper CSHE6-03. Berkeley, CA: Center for Studies in Higher Education, 2003, http://repositories.cdlib.org/cshe/CSHE6-03.
- Thomas Jefferson, Autobiography, MW 1:54.
- H. C. King, Education and the National Character (Chicago: The Religious Education Association, 1908).
- U.S. Department of Education, Institute of Education Sciences, Enrollment in Postsecondary Institutions, Fall 2004; Graduation Rates, 1998 & 2001 Cohorts; and Financial Statistics, Fiscal Year 2004 (Washington, DC: U.S. Government Printing Office, 2006), http://nces.ed.gov//pubs2006/2006155.pdf.
- Jeffrey Thomas, “First-Time International Student U.S. Enrollments Up 10.2 Percent,” America.gov, [http://www.america.gov/st/washfile-english/2007/November/200711131634391CJsamohT0.5697748.html] (November 13, 2007).
- See Education at a Glance, 2007, OECD Indicators (Organisation for Economic Co-operation and Development, 2007), 57, [http://www.sourceoecd.org/upload/9607051e.pdf] (data are from 2005). Across 24 OECD countries, 36% of students have completed baccalaureate-level education. This is an increase of 12 percentage points over the last decade. Graduation rates have doubled or more during the past 10 years in Austria, Finland, Portugal, the Slovak Republic, and Switzerland but have been stable in the United States, which, along with New Zealand, had the highest rate in 1995.
- Thomas L. Friedman, The World Is Flat: A Brief History of the Twenty-First Century (New York: Farrar, Straus, and Giroux, 2005).
- Richard Monastersky, “The Number That Is Devouring Science,” Chronicle of Higher Education (October 14, 2005): A12, https://www.chronicle.com/article/the-number-thats-devouring-science/.
- Elsa Wenzel, “Number of PC’s in Use to Hit 2 Billion by 2014,” SmartPlanet, posted June 24, 2008, [http://www.smartplanet.com/news/tech/10001448/number-of-pcs-in-use-to-hit-2-billion-by-2014.htm].
- Robert H. Zakon, “Hobbes’ Internet Timeline V8.2,” http://www.zakon.org/robert/internet/timeline. See also the Wikipedia description of “Wi-Fi” at http://en.wikipedia.org/wiki/Wi-Fi.
- Martin Trow argues that “IT is embedded in, and used by, institutions that have a history … . IT will cut its own channels, leading to the creation of institutions that differ from those of today; institutions where the weight of history does not condition and constrain IT’s use,” in “The Development of Information Technology in American Higher Education,” Daedalus 126, no. 4 (Fall 1997): 294. Stanley Katz, on the other hand, exhorts us not to mistake IT as a goal, rather than a tool. See Stanley N. Katz, “In Information Technology, Don’t Mistake a Tool for a Goal,” Chronicle of Higher Education (June 15, 2001), [http://chronicle.com/free/v47/i40/40b00701.htm].
- R. D. Laing, The Politics of Experience (New York: Pantheon Books, 1967).
- Grant McCracken, “The Cloudy Self: Or What Has Technology Done to Us,” posted to his blog, January 30, 2007, https://cultureby.com/2007/01/the_cloudy_self.html.
- Brown and Duguid, 9.
- On the democratization of IT, see Bruce Malloy, “‘Digital Natives’ Take Charge; Get Ready for the Democratization of IT,” New Jersey Tech News (June 2008): 12, [http://www.connotate.com/news/NJTech_080601_Democ_of_IT.pdf]. On the industrialization of IT, see Nicholas Carr, The Big Switch: Rewiring the World from Edison to Google (New York: W. W. Norton & Co., 2008).
- See the work of Nicholas Carr, such as his Harvard Business Review article “IT Doesn’t Matter,” The Digital Enterprise (Cambridge, MA: Harvard Business Press, 2001), The Big Switch, and others. Carr argues that as in the Industrial Revolution, when we moved from factory generation of power to power grids, so will we move from enterprise-based IT infrastructure to cloud-based IT services and infrastructure.'
- James Hilton, “The Future for Higher Education: Sunrise or Perfect Storm?,” EDUCAUSE Review (March/April 2006): 60, http://www.educause.edu/ir/library/pdf/ERM0623.pdf.
- Brown and Duguid, 15.
- Farhad Manjoo, True Enough: Learning to Live in a Post-Fact Society (Hoboken, NJ: John Wiley & Sons, 2008), 16.
- Ibid., 17–8.
- Chris Dede, “A Seismic Shift in Epistemology,” EDUCAUSE Review (May/June 2008): 80, http://www.educause.edu/ir/library/pdf/ERM0837.pdf.
- Chris Anderson, The Long Tail (New York: Hyperion, 2006).
- See B. G. Verghese, “Reflections on Gandhi,” Writings and Commentaries, http://www.bgverghese.com/YouthCadres.htm.
- Hilton, 64.
- James Neal, quoted on Google Library Project website, http://books.google.com/googlebooks/partners.html.
- Hilton, 64.
- Ibid., 66.
- Thomas Jefferson, letter to Isaac McPherson, August 13, 1813.
- John Gerstner, “Cyber Cowboy: Interview with John Perry Barlow,” Communication World, November 2005, [http://findarticles.com/p/articles/mi_m4422/is_n10_v12/ai_17772838/pg_2?tag=artBody;col1].
- Walsh, 31.
- Ibid., 44.
- John Henry Newman, The Idea of a University Defined and Illustrated (London: Longman’s, Green & Co., 1893). Derek Bok more recently proposed eight purposes of college in Our Underachieving Colleges (Princeton, NJ: Princeton University Press, 2006), 113–6.
- Yochai Benkler, The Wealth of Networks (Cambridge, MA: Harvard University Press, 2006).
- See Nicholas Carr, “Crash: Amazon’s S3 Utility Goes Down,” Rough Type, February 15, 2008, http://www.roughtype.com/archives/2008/02/amazons_s3_util.php. See also Jon Brodkin, “Loss of Customer Data Spurs Closure of Online Storage Service ‘The Linkup,’” The Industry Standard, August 11, 2008, [http://www.thestandard.com/news/2008/08/11/loss-customer-data-spurs-closure-linkup] , and Peter Bright, “Storms in the Clouds Leave Users Up Creek Without a Paddle,” Ars Technica, August 13, 2008, http://arstechnica.com/news.ars/post/20080813-storms-in-the-clouds-leave-users-up-creek-without-a-paddle.html.
- Margaret P. Eisenhauer, “Protecting Personal Information in Third Party Hands: An Overview of Legal Requirements,” PrivacyStudio.com, January 6, 2006.
- Benkler, 1.
- Benkler, 2.
- James Bryant Conant, Letter to the New York Times, August 13, 1945.
- Charles Vest, “Open Content and the Emerging Global Meta-University,” EDUCAUSE Review (May/June 2006): 30, http://www.educause.edu/ir/library/pdf/ERM0630.pdf.
- Sarah Lacy, “On-Demand Computing: A Brutal Slog,” Business Week, July 18, 2008, https://www.bloomberg.com/news/articles/2008-07-18/on-demand-computing-a-brutal-slogbusinessweek-business-news-stock-market-and-financial-advice.
Bibliography
Anderson, Chris. The Long Tail. New York: Hyperion, 2006.
Benkler, Yochai. The Wealth of Networks. Cambridge, MA: Harvard University Press, 2006.
Bok, Derek. Our Underachieving Colleges. Princeton, NJ: Princeton University Press, 2006.
Bright, Peter. “Storms in the Clouds Leave Users Up Creek Without a Paddle.” Ars Technica, August 13, 2008. http://arstechnica.com/news.ars/post/20080813-storms-in-the-clouds-leave-users-up-creek-without-a-paddle.html.
Brodkin, Jon. “Loss of Customer Data Spurs Closure of Online Storage Service ‘The Linkup.’” The Industry Standard, August 11, 2008. [http://www.thestandard.com/news/2008/08/11/loss-customer-data-spurs-closure-linkup].
Brown, John Seely, and Paul Duguid. The Social Life of Information. Cambridge, MA: Harvard University Press, 2000.
Bryant, James Conant. Letter to the New York Times, August 13, 1945.
Carr, Nicholas G. “Crash: Amazon’s S3 Utility Goes Down.” Rough Type, February 15, 2008. http://www.roughtype.com/archives/2008/02/amazons_s3_util.php.
Carr, Nicholas G. Does IT Matter? Information Technology and the Corrosion of Competitive Advantage. Cambridge, MA: Harvard Business Press, 2004.
Carr, Nicholas G. “IT Doesn’t Matter.” Harvard Business Review (May 2003).
Carr, Nicholas G. The Big Switch: Rewiring the World, from Edison to Google. New York: W. W. Norton & Company, 2008.
Carr, Nicholas G. The Digital Enterprise: How to Reshape Your Business for a Connected World. Cambridge, MA: Harvard Business Press, 2001.
Dede, Chris. “A Seismic Shift in Epistemology.” EDUCAUSE Review (May/June 2008): 80–1. http://www.educause.edu/ir/library/pdf/ERM0837.pdf.
Education at a Glance, 2007, OECD Indicators. Organisation for Economic Co-operation and Development, 2007. [http://www.sourceoecd.org/upload/9607051e.pdf].
Eisenhauer, Margaret P. “Protecting Personal Information in Third Party Hands: An Overview of Legal Requirements.” PrivacyStudio.com, January 6, 2006.
Friedman, Thomas L. The World Is Flat: A Brief History of the Twenty-First Century. New York: Farrar, Straus, and Giroux, 2005.
Gerstner, John. “Cyber Cowboy: Interview with John Perry Barlow.” Communication World, November 2005. [http://findarticles.com/p/articles/mi_m4422/is_n10_v12/ai_17772838/pg_2?tag=artBody;col1].
Hilton, James. “The Future for Higher Education: Sunrise or Perfect Storm?” EDUCAUSE Review (March/April 2006): 59–71. http://www.educause.edu/ir/library/pdf/ERM0623.pdf.
Jefferson, Thomas. Autobiography, MW 1:54.
Jefferson, Thomas. Letter to Isaac McPherson, August 13, 1813.
Jefferson, Thomas. Letter to Tench Coxe, 1795.
Katz, Stanley N. “In Information Technology, Don’t Mistake a Tool for a Goal.” Chronicle of Higher Education (June 15, 2001): B7. [http://chronicle.com/free/v47/i40/40b00701.htm].
King, H. C. Education and the National Character. Chicago: The Religious Education Association, 1908.
Lacy, Sarah. “On-Demand Computing: A Brutal Slog.” Business Week, July 18, 2008. https://www.bloomberg.com/news/articles/2008-07-18/on-demand-computing-a-brutal-slogbusinessweek-business-news-stock-market-and-financial-advice.
Laing, R. D. The Politics of Experience. New York: Pantheon Books, 1967.
Malloy, Bruce. “‘Digital Natives’ Take Charge; Get Ready for the Democratization of IT.” New Jersey Tech News (June 2008): 12–3. [http://www.connotate.com/news/NJTech_080601_Democ_of_IT.pdf].
Manjoo, Farhad. True Enough: Learning to Live in a Post-Fact Society. Hoboken, NJ: John Wiley & Sons, 2008.
McCracken, Grant. “The Cloudy Self: Or What Has Technology Done to Us.” Posted to his blog, January 30, 2007. https://cultureby.com/2007/01/the_cloudy_self.html.
Merson, John. The Genius That Was China: East and West in the Making of the Modern World. New York: Overlook Press, 1990.
Monastersky, Richard. “The Number That Is Devouring Science.” Chronicle of Higher Education (October 14, 2005). https://www.chronicle.com/article/the-number-thats-devouring-science/.
Newman, John Henry. The Idea of a University Defined and Illustrated. London: Longman’s, Green & Co., 1893.
Pfeffer, Thomas. Virtualization of Research Universities: Raising the Right Questions to Address Key Functions of the Institution. Paper CSHE6-03. Berkeley, CA: Center for Studies in Higher Education, 2003. http://repositories.cdlib.org/cshe/CSHE6-03.
Plato. “Phaedrus.” The Dialogues of Plato.
Thomas, Jeffrey. “First-Time International Student U.S. Enrollments Up 10.2 Percent.” America.gov, [http://www.america.gov/st/washfile-english/2007/November/200711131634391CJsamohT0.5697748.html] (November 13, 2007).
Trow, Martin. “The Development of Information Technology in American Higher Education,” Daedalus 126, no. 4 (Fall 1997).
U.S. Department of Education, Institute of Education Sciences. Enrollment in Postsecondary Institutions, Fall 2004; Graduation Rates, 1998 & 2001 Cohorts; and Financial Statistics, Fiscal Year 2004. Washington, DC: U.S. Government Printing Office, 2006. http://nces.ed.gov//pubs2006/2006155.pdf.
Verghese, B. G. “Reflections on Gandhi.” Writings and Commentaries.http://www.bgverghese.com/YouthCadres.htm.
Vest, Charles. “Open Content and the Emerging Global Meta-University.” EDUCAUSE Review (May/June 2006): 19–25. http://www.educause.edu/ir/library/pdf/ERM0630.pdf.
Wagar, W. Warren. H. G. Wells: Traversing Time. Middletown, CT: Wesleyan University Press, 2004.
Walsh, Diana Chapman. Envisioning the Future: Reflections from the 2015 Commission. Final Report. Wellesley, MA: Wellesley College, 2007. [http://www.wellesley.edu/PublicAffairs/President/DCW/Announcements/2015synopsis.pdf].
Wenzel, Elsa. “Number of PC’s in Use to Hit 2 Billion by 2014.” SmartPlanet, posted June 24, 2008. [http://www.smartplanet.com/news/tech/10001448/number-of-pcs-in-use-to-hit-2-billion-by-2014.htm].
Wikipedia, “Wi-Fi,” http://en.wikipedia.org/wiki/Wi-Fi.
Zakon, Robert H. “Hobbes’ Internet Timeline V8.2.” http://www.zakon.org/robert/internet/timeline.